Valid AZ-400 Dumps shared by PassLeader for Helping Passing AZ-400 Exam! PassLeader now offer the newest AZ-400 VCE dumps and AZ-400 PDF dumps, the PassLeader AZ-400 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader AZ-400 dumps with VCE and PDF here: https://www.passleader.com/az-400.html (240 Q&As Dumps –> 264 Q&As Dumps –> 296 Q&As Dumps –> 327 Q&As Dumps –> 366 Q&As Dumps –> 489 Q&As Dumps –> 513 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader AZ-400 dumps from Cloud Storage: https://drive.google.com/open?id=1L7kKrrFiEOHT2sXpAOJyL21YYGtCNOUZ
NEW QUESTION 220
Your company uses Azure Artifacts for package management. You need to configure an upstream source in Azure Artifacts for Python packages. Which repository type should you use as an upstream source?
A. npmjs.org
B. PyPI
C. Maven Central
D. third-party trusted Python
Answer: B
Explanation:
https://docs.microsoft.com/en-us/azure/devops/artifacts/quickstarts/python-packages
NEW QUESTION 221
Your company uses Azure DevOps to manage the build and release processes for applications. You use a Git repository for applications source control. You plan to create a new branch from an existing pull request. Later, you plan to merge the new branch and the target branch of the pull request. You need to use a pull request action to create the new branch. The solution must ensure that the branch uses only a portion of the code in the pull request. Which pull request action should you use?
A. Set as default branch
B. Approve with suggestions
C. Cherry-pick
D. Reactivate
E. Revert
Answer: C
Explanation:
https://docs.microsoft.com/en-us/azure/devops/repos/git/pull-requests
NEW QUESTION 222
You have an Azure DevOps organization named Contoso that contains a project named Project1. You provision an Azure key vault named Keyvault1. You need to reference Keyvault1 secrets in a build pipeline of Project1. What should you do first?
A. Add a secure file to Project1.
B. Create an XAML build service.
C. Create a variable group in Project1.
D. Configure the security policy of Contoso.
Answer: D
Explanation:
Before this will work, the build needs permission to access the Azure Key Vault. This can be added in the Azure Portal. Open the Access Policies in the Key Vault and add a new one. Choose the principle used in the DevOps build.
https://docs.microsoft.com/en-us/azure/devops/pipelines/release/azure-key-vault
NEW QUESTION 223
You are designing a build pipeline in Azure Pipelines. The pipeline requires a self-hosted agent. The build pipeline will run once daily and will take 30 minutes to complete. You need to recommend a compute type for the agent. The solution must minimize costs. What should you recommend?
A. an Azure Kubernetes Service (AKS) cluster
B. Azure Container Instances
C. an Azure virtual machine scale set
D. Azure virtual machines
Answer: B
Explanation:
If your pipelines are in Azure Pipelines, then you’ve got a convenient option to run your jobs using a Microsoft-hosted agent. With Microsoft-hosted agents, maintenance and upgrades are taken care of for you. Each time you run a pipeline, you get a fresh virtual machine. The virtual machine is discarded after one use. Microsoft-hosted agents can run jobs directly on the VM or in a container.
https://docs.microsoft.com/en-us/azure/devops/pipelines/agents/hosted
NEW QUESTION 224
Your company has an Azure DevOps project. The source code for the project is stored in an on-premises repository and uses on an on-premises build server. You plan to use Azure DevOps to control the build process on the build server by using a self-hosted agent. You need to implement the self-hosted agent. You download and install the agent on the build server. Which two actions should you perform next? (Each correct answer presents part of the solution. Choose two.)
A. From Azure, create a shared access signature (SAS).
B. From the build server, create a certificate, and then upload the certificate to Azure Storage.
C. From the build server, create a certificate, and then upload the certificate to Azure Key Vault.
D. From DevOps, create a personal access token (PAT).
E. From the build server, run config.cmd.
Answer: BE
Explanation:
B: Make sure you install your self-signed ssl server certificate into the OS certificate store.
E: When you have a self-signed SSL certificate for your on-premises TFS server, make sure to configure the Git we shipped to allow that self-signed SSL certificate.
https://docs.microsoft.com/en-us/azure/devops/pipelines/agents/certificate
NEW QUESTION 225
You have an Azure DevOps project that contains a build pipeline. The build pipeline uses approximately 50 open source libraries. You need to ensure that all the open source libraries comply with your company’s licensing standards. Which service should you use?
A. Ansible
B. Maven
C. WhiteSource Bolt
D. Helm
Answer: C
Explanation:
WhiteSource provides WhiteSource Bolt, a lightweight open source security and management solution developed specifically for integration with Azure DevOps and Azure DevOps Server.
https://www.azuredevopslabs.com/labs/vstsextend/whitesource/
NEW QUESTION 226
Your company develops an application named App1 that is deployed in production. As part of an application update, a new service is being added to App1. The new service requires access to an application named App2 that is currently in development. You need to ensure that you can deploy the update to App1 before App2 becomes available. You must be able to enable the service in App1 once App2 is deployed. What should you do?
A. Implement a feature flag.
B. Create a fork in the build.
C. Create a branch in the build.
D. Implement a branch policy.
Answer: A
Explanation:
Feature flags support a customer-first DevOps mindset, to enable (expose) and disable (hide) features in a solution, even before they are complete and ready for release.
Incorrect:
Not C: Branch policies are an important part of the Git workflow and enable you to:
– Isolate work in progress from the completed work in your master branch.
– Guarantee changes build before they get to master.
https://docs.microsoft.com/en-us/azure/devops/migrate/phase-features-with-feature-flags
NEW QUESTION 227
You are designing the security validation strategy for a project in Azure DevOps. You need to identify package dependencies that have known security issues and can be resolved by an update. What should you use?
A. Octopus Deploy
B. Jenkins
C. Gradle
D. SonarQube
Answer: A
Explanation:
Incorrect:
Not B: Jenkins is a popular open-source automation server used to set up continuous integration and delivery (CI/CD) for your software projects.
Not D: SonarQube is a set of static analyzers that can be used to identify areas of improvement in your code. It allows you to analyze the technical debt in your project and keep track of it in the future.
https://octopus.com/docs/packaging-applications
NEW QUESTION 228
You have a private distribution group that contains provisioned and unprovisioned devices. You need to distribute a new iOS application to the distribution group by using Microsoft Visual Studio App Center. What should you do?
A. Generate a new .p12 file for each device.
B. Create an unsigned build.
C. Register the devices on the Apple Developer portal.
D. Create an active subscription in App Center Test.
Answer: C
Explanation:
When releasing an iOS app signed with an ad-hoc or development provisioning profile, you must obtain tester’s device IDs (UDIDs), and add them to the provisioning profile before compiling a release. When you enable the distribution group’s Automatically manage devices setting, App Center automates the before mentioned operations and removes the constraint for you to perform any manual tasks. As part of automating the workflow, you must provide the user name and password for your Apple ID and your production certificate in a .p12 format. App Center starts the automated tasks when you distribute a new release or one of your testers registers a new device. First, all devices from the target distribution group will be registered, using your Apple ID, in your developer portal and all provisioning profiles used in the app will be generated with both new and existing device ID. Afterward, the newly generated provisioning profiles are downloaded to App Center servers.
https://docs.microsoft.com/en-us/appcenter/distribution/groups
NEW QUESTION 229
Your company uses the following resources:
– Windows Server 2019 container images hosted in an Azure Container Registry.
– Azure virtual machines that run the latest version of Ubuntu.
– An Azure Log Analytics workspace.
– Azure Active Directory (Azure AD).
– An Azure key vault.
For which two resources can you receive vulnerability assessments in Azure Security Center? (Each correct answer presents part of the solution. Choose two.)
A. the Azure Log Analytics workspace
B. the Azure key vault
C. the Azure virtual machines that run the latest version of Ubuntu
D. Azure Active Directory (Azure AD)
E. the Windows Server 2019 container images hosted in the Azure Container Registry
Answer: BC
Explanation:
B: Azure Security Center includes Azure-native, advanced threat protection for Azure Key Vault, providing an additional layer of security intelligence.
C: When Security Center discovers a connected VM without a vulnerability assessment solution deployed, it provides the security recommendation “A vulnerability assessment solution should be enabled on your virtual machines”.
https://docs.microsoft.com/en-us/azure/security-center/deploy-vulnerability-assessment-vm
NEW QUESTION 230
You have a private project in Azure DevOps. You need to ensure that a project manager can create custom work item queries to report on the project’s progress. The solution must use the principle of least privilege. To which security group should you add the project manager?
A. Reader
B. Project Collection Administrators
C. Project Administrators
D. Contributor
Answer: D
Explanation:
Contributors have permissions to contribute fully to the project code base and work item tracking. The main permissions they don’t have or those that manage or administer resources.
https://docs.microsoft.com/en-us/azure/devops/organizations/security/permissions
NEW QUESTION 231
You have an Azure DevOps organization named Contoso and an Azure subscription. You use Azure DevOps to build and deploy a web app named App1. Azure Monitor is configured to generate an email notification in response to alerts generated whenever App1 generates a server-side error. You need to receive notifications in Microsoft Teams whenever an Azure Monitor alert is generated. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Create an Azure Monitor workbook.
B. Create an Azure logic app that has an HTTP request trigger.
C. Create an Azure logic app that has an Azure DevOps trigger.
D. Modify an action group in Azure Monitor.
E. Modify the Diagnostics settings in Azure Monitor.
Answer: CD
Explanation:
https://dirteam.com/dave/2019/05/14/getting-azure-devops-tasks-in-to-do-with-flow/
NEW QUESTION 232
You are designing a strategy to monitor the baseline metrics of Azure virtual machines that run Windows Server. You need to collect detailed data about the processes running in the guest operating system. Which two agents should you deploy? (Each correct answer presents part of the solution. Choose two.)
A. the Telegraf agent
B. the Azure Log Analytics agent
C. the Azure Network Watcher Agent for Windows
D. the Dependency agent
Answer: BD
Explanation:
https://docs.microsoft.com/en-us/azure/azure-monitor/platform/agents-overview
NEW QUESTION 233
You configure an Azure Application Insights availability test. You need to notify the customer services department at your company by email when availability is degraded. You create an Azure logic app that will handle the email and follow up actions. Which type of trigger should you use to invoke the logic app?
A. an HTTPWebhook trigger
B. an HTTP trigger
C. a Request trigger
D. an ApiConnection trigger
Answer: A
Explanation:
You can use webhooks to route an Azure alert notification to other systems for post-processing or custom actions. You can use a webhook on an alert to route it to services that send SMS messages, to log bugs, to notify a team via chat or messaging services, or for various other actions.
https://docs.microsoft.com/en-us/azure/azure-monitor/platform/alerts-webhooks
NEW QUESTION 234
You have an Azure DevOps organization named Contoso and an Azure subscription. You use Azure DevOps to build a containerized app named App1 and deploy App1 to an Azure container instance named ACI1. You need to restart ACI1 when App1 stops responding. What should you do?
A. Add a liveness probe to the YAML configuration of App1.
B. Add a readiness probe to the YAML configuration of App1.
C. Use Connection Monitor in Azure Network Watcher.
D. Use IP flow verify in Azure Network Watcher.
Answer: B
Explanation:
For containerized applications that serve traffic, you might want to verify that your container is ready to handle incoming requests. Azure Container Instances supports readiness probes to include configurations so that your container can’t be accessed under certain conditions. The readiness probe behaves like a Kubernetes readiness probe. For example, a container app might need to load a large data set during startup, and you don’t want it to receive requests during this time. YAML is used to setup a liveness probe.
https://docs.microsoft.com/en-us/azure/container-instances/container-instances-readiness-probe
NEW QUESTION 235
Drag and Drop
You manage the Git repository for a large enterprise application. During the development of the application, you use a file named Config.json. You need to prevent Config.json from being committed to the source control whenever changes to the application are committed. Which three actions should you perform in sequence? (To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.)

Answer:

Explanation:
Step 1: Delete and recreate the repository.
Step 2: Add Config.json to the .gitignore file. Each line in the .gitignore excludes a file or set of files that match a pattern.
Step 3: Run the git add .gitignore command. At the initial commit we want basically move from Untracked to Staged, for staging we have to indicate which file we want to move or specify a pattern.
http://hermit.no/how-to-find-the-best-gitignore-for-visual-studio-and-azure-devops/
https://geohernandez.net/how-to-add-an-existing-repository-into-azure-devops-repo-with-git/
NEW QUESTION 236
Hotspot
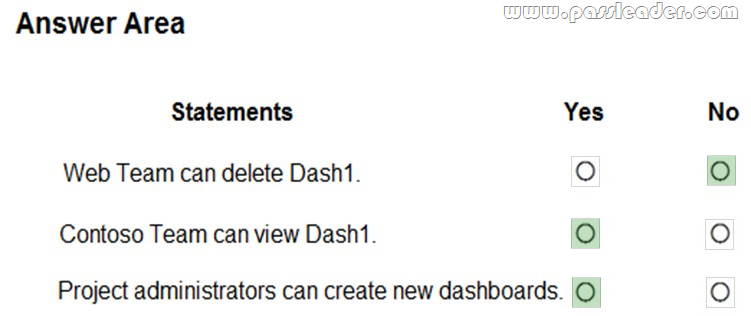
You have a project in Azure DevOps that has three teams as shown in the Teams exhibit:

You create a new dashboard named Dash1. You configure the dashboard permissions for the Control project as shown in the Permissions exhibit:
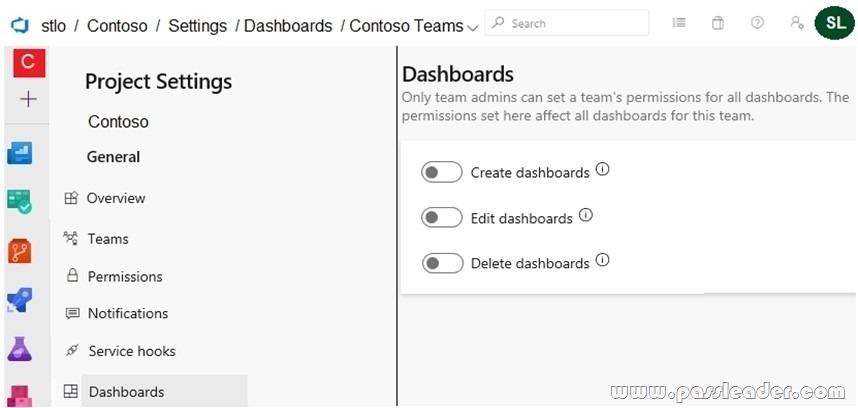
All other permissions have the default values set. For each of the following statements, select Yes if the statement is true. Otherwise, select No.
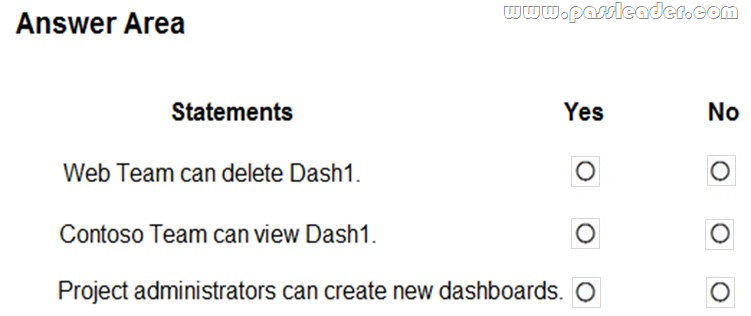
Answer:
Explanation:
https://docs.microsoft.com/en-us/azure/devops/report/dashboards/charts-dashboard-permissions-access
NEW QUESTION 237
……
Get the newest PassLeader AZ-400 VCE dumps here: https://www.passleader.com/az-400.html (240 Q&As Dumps –> 264 Q&As Dumps –> 296 Q&As Dumps –> 327 Q&As Dumps –> 366 Q&As Dumps –> 489 Q&As Dumps –> 513 Q&As Dumps)
And, DOWNLOAD the newest PassLeader AZ-400 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=1L7kKrrFiEOHT2sXpAOJyL21YYGtCNOUZ