Valid AZ-500 Dumps shared by PassLeader for Helping Passing AZ-500 Exam! PassLeader now offer the newest AZ-500 VCE dumps and AZ-500 PDF dumps, the PassLeader AZ-500 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader AZ-500 dumps with VCE and PDF here: https://www.passleader.com/az-500.html (306 Q&As Dumps –> 367 Q&As Dumps –> 438 Q&As Dumps –> 548 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader AZ-500 dumps from Cloud Storage: https://drive.google.com/open?id=1CnqNGckypCByp19q05gCYQD-Qai7gnHt
NEW QUESTION 291
You have an Azure Sentinel deployment. You need to create a scheduled query rule named Rule1. What should you use to define the query rule logic for Rule1?
A. a Transact-SQL statement
B. a JSON definition
C. GraphQL
D. a Kusto query
Answer: D
Explanation:
https://docs.microsoft.com/en-us/azure/sentinel/tutorial-detect-threats-custom
NEW QUESTION 292
You have an Azure subscription that is linked to an Azure Active Directory (Azure AD) tenant. From the Azure portal, you register an enterprise application. Which additional resource will be created in Azure AD?
A. a service principal
B. an X.509 certificate
C. a managed identity
D. a user account
Answer: A
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory/develop/active-directory-how-applications-are-added
NEW QUESTION 293
Your company has an Azure SQL database. The database also consists of sensitive data. You want the prevent sensitive data from appearing as plain text inside the database system. What would be your step of action?
A. Configure Dynamic Data Masking (DDM).
B. Enable Advanced Data Security (ADS).
C. Configure Always Encrypted.
D. Enable Transparent Data Encryption (TDE).
Answer: C
NEW QUESTION 294
Your organization has a Microsoft SQL Server 2019 database. The database is hosted on an Azure virtual machine (VM). There is a web application that uses the database as its data store. The page speed of customers shopping is cart is noticeably slow. What will you do if you want tp know what stored is being called when customers access this page?
A. Choose Display Estimated Execution Plan from the Query menu.
B. Choose Include Actual Execution Plan from the Query menu.
C. Create a SQL Server Profiler trace.
D. Call the SET SHOWPLAN TEXT statement in Query Analyzer.
Answer: C
NEW QUESTION 295
You work for a company running five Windows Server 2012 R2 virtual machines (VMs). The VMs are located in the Azure West Europe region. The VMs were originally deployed from the Azure marketplace. There is presently a n antivirus solution installed and is expected to become end of life soon. The company wants to now replace the old antivirus solution with Microsoft Antimalware. You are required to enable Microsoft Antimalware on each VM and do it with zero manual interaction. What would be your next step of action?
A. Add the Microsoft Antimalware extension on each VM using the Azure portal.
B. Download the Microsoft Antimalware MSI package and install it manually on each VM.
C. Use the Install-WindowsFeature command on each VM to install the Microsoft Antimalware feature.
D. Download the Microsoft Antimalware MSI package and install it on each VM by using the Desired State Configuration (DSC).
Answer: A
NEW QUESTION 296
There are six Azure virtual machines (VMs)in your organization. The VMs are running Linux. Your organization has a line-of-business (LOB) application and these six VMs form the web tier of this LOB application. You want the key application services to start programmatically. Which of the following do you think you should use?
A. Application security group (ASG).
B. Custom script extension.
C. Webjob.
D. Login App.
Answer: B
NEW QUESTION 297
Your organization stores Docker images for internal development using Azure Container Registry. You are required to configure the registry in such a way that a registry name is needed by developers to log into the registry and an access key is required as the password. What would be your step of action?
A. Create a system-assigned managed identity.
B. Define a service endpoint for the registry.
C. Assign the developers to the AcrPull role-based access control (RBAC) role.
D. Enable the admin user in the registry.
Answer: D
NEW QUESTION 298
VNet1 is an Azure virtual network (VNet) where several development servers of the company are running. There development team has numerous Docker images stored in a private repository. These container images are planned to be deployed in Azure using Azure Container Instances (ACI). You need to restrict access to these containers to VNet1. What will be your next step of action?
A. Deploy the container instances into VNet1.
B. Use a managed identity with the container instances.
C. Modify the role-based access control (RBAC) permissions on the container instances.
D. Add a Domain Name System (DNS) name label to each container instance.
Answer: A
NEW QUESTION 299
You have an Azure subscription that contains the resources shown in the following table:

You need to ensure that ServerAdmins can perform the following tasks:
– Create virtual machines in RG1 only.
– Connect the virtual machines to the existing virtual networks in RG2 only.
The solution must use the principle of least privilege. Which two role-based access control (RBAC) roles should you assign to ServerAdmins? (Each correct answer presents part of the solution. Choose two.)
A. a custom RBAC role for RG2
B. the Network Contributor role for RG2
C. the Contributor role for the subscription
D. a custom RBAC role for the subscription
E. the Network Contributor role for RG1
F. the Virtual Machine Contributor role for RG1
Answer: AF
Explanation:
https://docs.microsoft.com/en-us/azure/role-based-access-control/built-in-roles
NEW QUESTION 300
You have an Azure subscription named Subscription1 that contains a resource group named RG1 and the users shown in the following table:

You perform the following tasks:
– Assign User1 the Network Contributor role for Subscription1.
– Assign User2 the Contributor role for RG1.
To Subscription1 and RG1, you assign the following policy definition: External accounts with write permissions should be removed from your subscription. What is the Compliance State of the policy assignments?
A. The Compliance State of both policy assignments is Non-compliant.
B. The Compliance State of the policy assignment to Subscription1 is Compliant, and the Compliance State of the policy assignment to RG1 is Non-compliant.
C. The Compliance State of the policy assignment to Subscription1 is Non-compliant, and the Compliance State of the policy assignment to RG1 is Compliant.
D. The Compliance State of both policy assignments is Compliant.
Answer: A
NEW QUESTION 301
HotSpot
You have an Azure Sentinel workspace that has the following data connectors:
– Azure Active Directory Identity Protection
– Common Event Format (CEF)
– Azure Firewall
You need to ensure that data is being ingested from each connector. From the Logs query window, which table should you query for each connector? (To answer, select the appropriate options in the answer area.)

Answer:
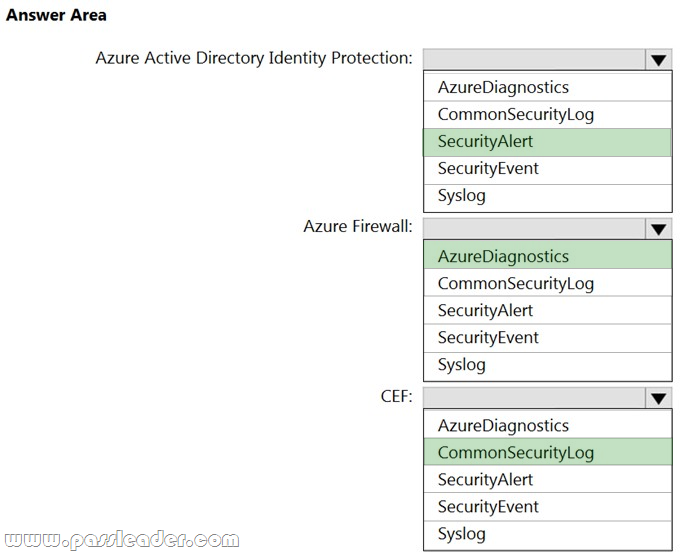
Explanation:
https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-ad-identity-protection
https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-firewall
https://docs.microsoft.com/en-us/azure/sentinel/connect-data-sources
NEW QUESTION 302
Drag and Drop
You have an Azure subscription. You plan to create a storage account. You need to use customer-managed keys to encrypt the tables in the storage account. From Azure Cloud Shell, which three cmdlets should you run in sequence? (To answer, move the appropriate cmdlets from the list of cmdlets to the answer area and arrange them in the correct order.)

NEW QUESTION 303
……
Get the newest PassLeader AZ-500 VCE dumps here: https://www.passleader.com/az-500.html (306 Q&As Dumps –> 367 Q&As Dumps –> 438 Q&As Dumps –> 548 Q&As Dumps)
And, DOWNLOAD the newest PassLeader AZ-500 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=1CnqNGckypCByp19q05gCYQD-Qai7gnHt
