Valid 70-243 Dumps shared by PassLeader for Helping Passing 70-243 Exam! PassLeader now offer the newest 70-243 VCE dumps and 70-243 PDF dumps, the PassLeader 70-243 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-243 dumps with VCE and PDF here: http://www.passleader.com/70-243.html (185 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-243 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpfmVaZDlXWUtVTTZVWWQ1Z3ZHdk1Gb0pBbWN4V2VOclZqcnFaUk5udTRUeGc
QUESTION 61
Hotspot Question
Your network contains a System Center 2012 Configuration Manager environment. You deploy an application to 1,000 client computers. You need to identify which client computers are in the process of installing the application. Which node should you select in the Configuration Manager console? To answer, select the appropriate node in the answer area.
Answer:
Explanation:
http://technet.microsoft.com/en-us/library/gg682201
How to Monitor Applications in Configuration Manager.
In Microsoft System Center 2012 Configuration Manager, you can monitor the deployment of all software, including software updates, compliance settings, applications, task sequences, and packages and programs. You can monitor deployments by using the Monitoring workspace in the Configuration Manager console or by using reports. Applications in Configuration Manager support state-based monitoring, which allows you to track the last application deployment state for users and devices. These state messages display information about individual devices. For example, if an application is deployed to a collection of users, you can view the compliance state of the deployment and the deployment purpose in the Configuration Manager console. An application deployment state has one of the following compliance states:
* Success – The application deployment succeeded or was found to be already installed.
* In Progress – The application deployment is in progress.
* Unknown – The state of the application deployment could not be determined. This state is not applicable for deployments with a purpose of Available. This state is typically displayed when state messages from the client are not yet received.
* Requirements Not Met – The application was not deployed because it was not compliant with a dependency or a requirement rule, or because the operating system to which it was deployed was not applicable.
* Error – The application failed to deploy because of an error.
To monitor the state of an application in the Configuration Manager console:
* In the Configuration Manager console, click Monitoring.
* In the Monitoring workspace, click Deployments.
– To review deployment details for each compliance state and the devices in that state, select a deployment, and then, on the Home tab, in the Deployment group, click View Status to open the Deployment Status pane. In this pane, you can view the assets with each compliance state. Click any asset to view more detailed information about the deployment status to that asset.
– To review general status information about an application deployment, select a deployment, and then click the Summary tab in the Selected Deployment window.
– To review information about the applications deployment type, select a deployment, and then click the Deployment Types tab in the Selected Deployment window.
QUESTION 62
Your network contains a System Center 2012 Configuration Manager environment. Software Inventory and Hardware Inventory are enabled for all client computers. All of the client computers have an application named App1 installed. App1 saves files to the C:\Program Files\App1 folder. All of the files saved by App1 have a file name extension of .xyz. You configure Software Inventory to inventory all of the files that have the .xyz extension and the .exe extension. After six months, you discover that some of the client computers fail to inventory .xyz files. All of the client computers inventory .exe files. You need to ensure that the .xyz files are inventoried. What should you do?
A. Modify C:\Program Files\App1\Skpswi.dat.
B. Modify C:\NO_SMS_On_Drive.sms.
C. Delete C:\Program Files\App1\Skpswi.dat.
D. Delete C:\NO_SMS_On_Drive.sms.
Answer: C
Explanation:
http://technet.microsoft.com/en-us/library/hh691018.aspx
How to Exclude Folders from Software Inventory in Configuration Manager.
You can create a hidden file named Skpswi.dat and place it in the root of a client hard drive to exclude it from System Center 2012 Configuration Manager software inventory. You can also place this file in the root of any folder structure you want to exclude from software inventory. This procedure can be used to disable software inventory on a single workstation or server client, such as a large file server. Note: Software inventory will not inventory the client drive again unless this file is deleted from the drive on the client computer.
QUESTION 63
Your network contains a System Center 2012 Configuration Manager environment. You deploy the Configuration Manager client to all client computers. You enable Hardware Inventory and Software Inventory for all of the client computers. You discover that one of the client computers fails to report inventory data. You confirm that the inventory files are copied correctly to the site server. You discover, however, that the site server does not contain any data from the client computer. You need to identify what is causing the reporting issue. Which log file should you review?
A. Dataldr.log
B. Inventoryagent.log
C. Mp_hinv.log
D. Contenttransfermanager.log
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/hh427342.aspx
Technical Reference for Log Files in Configuration Manager.
– Dataldr.log: Site Server log file. Records information about the processing of Management Information Format (MIF) files and hardware inventory in the Configuration Manager database.
– MP_Hinv.log: Site system server log file. Records details about the conversion of XML hardware inventory records from clients and the copy of those files to the site server.
– InventoryAgent.log: Client log file. Records activities of hardware inventory, software inventory, and heartbeat discovery actions on the client.
– ContentTransferManager.log: Client log file. Schedules the Background Intelligent Transfer Service (BITS) or the Server Message Block (SMB) to download or to access packages.
Further information:
http://technet.microsoft.com/en-us/library/bb932206.aspx
Troubleshooting Configuration Manager Performance.
Slow Hardware Inventory Processing – Solution.
If you suspect that hardware inventory report processing is slow for a Configuration Manager 2007 site, the following actions should be taken:
1. Inspect the client inventoryagent.log log file to determine whether the client is sending delta hardware inventory reports or full reports. After initial client deployment, a very high percentage of hardware inventory reports should be deltas, which contain much less data than full inventory reports. If you are seeing a significant number of full inventory reports, this could be caused by inconsistent inventory report processing by the site server. For example, a delta hardware inventory report could be processed before a full inventory report for the same system has been processed. In this situation, a hardware inventory resynchronization request will be sent to the client and an additional full inventory report will be generated. To determine whether this is happening, review the dataldr.log log file on the site server.
2. Inspect the size of the hardware inventory files in the site server’s inbox directory to determine whether the software inventory files have grown significantly from previous inventory reports. If hardware inventory report file sizes have grown beyond an initial hardware inventory report file size baseline, you should determine the cause and whether the larger inventory report files are expected to be larger. One possibility is that the site’s SMS_def.mof file has been modified to collect more inventory information from clients.
3. Determine whether there is a consistent SMS_def.mof hardware inventory reporting file in use throughout the hierarchy. If not, the hardware inventory processor might be running very slowly because of changes in the database schema caused by the different SMS_def.mof files throughout the hierarchy. The dataloader.log log file will record instances of database schema changes and should be reviewed when investigating this issue.
http://technet.microsoft.com/en-us/library/cc723597.aspx
Chapter 20 – Hardware and Software Inventory Flowcharts.
– If a backlog of MIF files accumulates at the site server (that is, if MIF files are not being processed):
*. Examine the Inventory Data Loader status messages or the Dataldr.log file to determine whether the Inventory Data Loader has been able to connect to the SMS site database server. Inventory Data Loader might be unable to write a discovered client’s MIF to the database.
– If the MIF files are not being processed on the site server:
* Verify that Inventory Data Loader successfully parsed the MIF file by checking Inventory Data Loader status messages or the Dataldr.log file. If the MIF file cannot be processed, it will be transferred to the \Badmifs directory.
– If inventory from clients is not being reported to a new parent site:
* Examine the Dataldr.log file to verify that Inventory Data Loader has read the *.sha file, stopped all new MIF file processing, and is creating MIF files for each client’s data in the site database to forward to the parent site.
QUESTION 64
Note: This question is part of a series of questions that use the same set of answer choices. An answer choice may be correct for more than one question in the series. Your network contains a System Center 2012 Configuration Manager environment. The network contains 10 database servers that run Microsoft SQL Server 2008. You have a configuration baseline that is used to monitor the database servers. You confirm that all of the database servers downloaded the configuration baseline. You discover that a database server named Server1 fails to report any data for the configuration baseline. You need to identify whether Server1 evaluates the configuration items that are part of the configuration baseline. Which log file should you review?
A. Ciagent.log
B. Sitestat.log
C. Ccm.log
D. Rcmctrl.log
E. Smsexec.log
F. Dcmagent.log
G. Hman.log
H. Contenttransfermanager.log
I. Sdmagent.log
J. Wsyncmgr.log
K. Locationservices.log
Answer: F
Explanation:
http://technet.microsoft.com/en-us/library/hh427342.aspx
DCMAgent.log: Records high-level information about the evaluation, conflict reporting, and remediation of configuration items and applications.
QUESTION 65
Note: This question is part of a series of questions that use the same set of answer choices. An answer choice may be correct for more than one question in the series.
Your network contains a System Center 2012 Configuration Manager environment. You add a software update point to the environment. You receive a message indicating that SMS WSUS Synchronization failed. You need to retrieve additional information about the message. Which log file should you review?
A. Ciagent.log
B. Contenttransfermanager.log
C. Sdmagent.bg
D. Dcmagent.log
E. Locationservices.log
F. Wsyncmgr.log
G. Rcmctrl.log
H. Ccm.log
I. Sitestat.log
J. Smsexec.log
K. Hman.log
Answer: F
Explanation:
http://technet.microsoft.com/en-us/library/hh427342.aspx
Wsyncmgr.log: Records details about the software updates synchronization process.
QUESTION 66
Note: This question is part of a series of questions that use the same set of answer choices. An answer choice may be correct for more than one question in the series.
You enable Client Push. You run Active Directory System Discovery. You discover that some of the discovered computers do not have the System Center 2012 Configuration Manager client installed. You need to identify why Client Push fails on some of the client computers. Which log file should you review?
A. Sdmagent.log
B. Dcmagent.log
C. Rcmctrl.log
D. Smsexec.log
E. Locationservices.log
F. Contenttransfermanager.log
G. Ccm.log
H. Wsyncmgr.log
I. sitestat.log
J. Ciagent.log
K. Hman.log
Answer: G
Explanation:
http://technet.microsoft.com/en-us/library/hh427342.aspx
Ccm.log: Records client push installation activities.
QUESTION 67
Drag and Drop Question
Your network contains a System Center 2012 Configuration Manager environment. Three users named User1, User2, and User3 will perform the following tasks:
– User1 will review software metering data and inventory reports.
– User2 will deploy applications and create alerts.
– User3 will deploy applications and create distribution point groups.
You need to identify which security role must be assigned to which user. What should you identify? To answer, drag the appropriate security role to the correct user in the answer area. Each security role may be used once, more than once, or not at all. Additionally, you may need to drag the split bar between panes or scroll to view content.
Answer: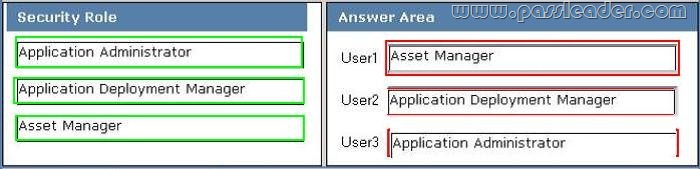
Explanation:
Application Administrator. This security role:
– Provides permissions included in both the Application Author and Application Deployment Manager roles.
– Provides permissions to manage queries, read and modify site permissions, manage collections, and manage settings for user device affinity.
Application Deployment Manager. This security role provides permissions to:
– View applications and manage deployments, alerts, templates, packages, and programs.
– View collections and their members, status messages, queries, and conditional delivery rules.
Asset Manager. This security role provides permissions to manage hardware and software inventory, software metering, and the Asset Intelligence reporting classes.
QUESTION 68
Your network contains a System center 2012 Configuration Manager environment. The environment contains a reporting services point. A group of users is responsible for creating custom reports. The custom reports will be published. You need to identify which tools can be used to create and publish custom reports to Microsoft SQL Server Reporting Services (SSRS). Which tools should you identify?
A. Reporting Services Configuration Manager
B. Microsoft SQL Server Management Studio
C. Microsoft SQL Server Business Intelligence Development Studio
D. Microsoft Access 2010 and Reporting Services Configuration Manager
Answer: C
Explanation:
http://technet.microsoft.com/en-us/library/gg508710.aspx
Overview of Custom Reports.
Custom reports are intended for advanced users who are comfortable creating their own reports by using Microsoft SQL Server Reporting Services and SQL Server Business Intelligence Development Studio, SQL Server Reporting Services Report Builder, or Microsoft Visual Studio Report Designer.
Further information:
http://msdn.microsoft.com/en-us/library/ms155792(v=sql.100)
Reporting Services Components and Tools.
http://msdn.microsoft.com/en-us/library/ms345231.aspx
Custom Report Items.
http://msdn.microsoft.com/en-us/library/ms345253
Custom Report Item Implementation Requirements.
http://technet.microsoft.com/en-us/library/gg682105.aspx
Introduction to Reporting in Configuration Manager.
http://technet.microsoft.com/en-us/library/hh338693.aspx
Creating Custom Report Models in SQL Server Reporting Services.
QUESTION 69
Your network contains a System Center 2012 Configuration Manger environment. You wirte the following query:
select SYS.Name from SMS_R_System SYS
join SMS_G_System_ADD_REMOVE_PROGRAMS ARP
on ARP.ResourceID = SYS.ResourceId
You need to create a list of all the client computers that have a version of Microsoft Office installed. What should you add to the query?
A. where ARP.DisplayName like “Microsoft Office*”
B. where ARP.DisplayName = “Microsoft Office*”
C. where ARP.DisplayName like “Microsoft Office%”
D. where ARP.DisplayName = “%Microsoft Office”
Answer: C
Explanation:
http://technet.microsoft.com/en-us/library/bb694123
For relational operators that perform LIKE comparisons (“is like” or “is not like”), you can use wildcard characters within the string. You can use the following wildcards:
Wildcard Description
%
Any string of zero or more characters
_ (underscore)
Any single character
[]
Any single character within the range or set (for example [a-f] or [abcdef]) [^]
Any single character not within the specified range (for example [^a-f] or [^abcdef])
QUESTION 70
You need to detect whether Office 2010 is installed before validating the configuration item. What should you do?
A. Create a query-based collection.
B. Create an automatic deployment rule.
C. Enable Use Windows Installer detection.
D. Create a report to display all installed software.
Answer: C
Explanation:
* Here are the basic steps for adding a Windows Installer detection method:
1. From the Deployment Type Properties dialog, select the Detection Method tab, and click Add Clause.
2. Choose the appropriate setting type. In this case, select Windows Installer , and click the Browse button.
3. Navigate to the desired .msi file and select Open. The product code appears, as By default, the rule looks for only the product code.
4. Click OK to save the detection rule.
* Example:
QUESTION 71
Note: This question is part of a series of questions that use the same set of answer choices. An answer choice may be correct for more than one question in the series.
Your network contains a System Center 2012 Configuration Manager environment. Your company deploys 1,000 client computers. You discover that information about printers fails to appear in any inventory queries or reports. Information about other hardware devices appears in the inventory queries and reports. You need to ensure that Configuration Manager data includes information about printers. What should you do?
A. Enable a default WMI class in the Hardware Inventory Classes list.
B. Add a file name to Software Metering.
C. Add a file name to the Hardware Inventory configuration.
D. Add a WMI class to the Sms_def.mof file.
E. Select Collect NOIDMIF files in Hardware Inventory.
F. Modify the Enable software inventory on clients setting.
G. Add a file name to the Software Inventory configuration.
H. Modify the Enable hardware inventory on clients setting.
I. Add a WMI class to the Hardware Inventory Classes list.
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/gg712290.aspx
How to Extend Hardware Inventory in Configuration Manager.
System Center 2012 Configuration Manager hardware inventory reads information about devices by using Windows Management Instrumentation (WMI). WMI is the Microsoft implementation of web-based Enterprise Management (WBEM), which is an industry standard for accessing management information in an enterprise environment. In previous versions of Configuration Manager, you could extend hardware inventory by modifying the file sms_def.mof on the site server. In System Center 2012 Configuration Manager, you no longer edit the sms_def.mof file as you did in Configuration Manager 2007. Instead, you can enable and disable WMI classes, and add new classes to collect by hardware inventory by using client settings. Configuration Manager provides the following methods to extend hardware inventory:
* Enable or disable existing inventory classes – You can enable or disable the default inventory classes used by Configuration Manager or you can create custom client settings that allow you to collect different hardware inventory classes from specified collections of clients.
* Add a new inventory class – You can add a new inventory class from the WMI namespace of another device.
* Import and export hardware inventory classes – You can import and export Managed Object Format (MOF) files that contain inventory classes from the Configuration Manager console.
* Create NOIDMIF Files – Use NOIDMIF files to collect information about client devices that cannot be inventoried by Configuration Manager.
* Create IDMIF Files – Use IDMIF files to collect information about assets in your organization that are not associated with a Configuration Manager client, for example, projectors, photocopiers and network printers.
Further information:
QUESTION 72
Your network contains a System Center 2012 Configuration Manager environment. The environment contains a single primary site. The primary site has a distribution point and a management point. You need to recommend a communication solution that meets the following requirements:
– Communication between the client computers in the research department and the management point must use HTTPS.
– Communication between all of the other client computers and the management point must be able to use HTTP.
– Minimize the number of site systems.
What should you do?
A. Configure the existing management point to use HTTPS.
Configure the research department computers always to use HTTPS.
B. Install a new management point and configure the management point always to use HTTPS.
Configure the research department computers always to use HTTPS.
C. Create a new primary child site and configure the site to use native mode.
Assign all of the research department computers to the new site.
D. Install a new management point and configure Windows Firewall to block inbound TCP port 80.
Configure the research department computers always to use HTTPS.
Answer: B
Explanation:
You can have one management point that accepts HTTPS client communication and another management point that accepts HTTP client communication. Note: To communicate with a site system role, the client must first locate a site system support the protocol (HTTPS or HTTP) that the client can use. By default, clients use the most secure method available to them. Using HTTPS before it communicates with a site system role that uses HTTP. When you deploy a site system role includemanagement points, anApplication Catalog website point, astate migration point, or distribution points, you must specify whether clients connect to the site system by using HTTP or HTTPS. If you use HTTP, you must also consider signing and encryption choices. In a single site, you can have one management point that accepts HTTPS client communication and another management point that accepts HTTP client communication. You can use one site to manage clients across different network locations that use different communication protocols and security settings. Other client computers can be configured for Internet and intranet client management. They can automatically switch between Internet-based client management and intranet client management when they detect a change of network. If these clients can find and connect to a management point that is configured for client connections on the intranet, they attempt to connect to an Internet-based management point.
Planning for Intrasite Communications in Configuration Manager.
URL:http://technet.microsoft.com/en-us/library/gg712701#Planning_Intra_site_Com
QUESTION 73
You deploy Windows 7 by using Operating System Deployment (OSD). The deployment task sequence contains steps to install software updates and applications. The amount of time required to deploy the Windows 7 image has increased significantly during the last six months. You need to recommend a solution to reduce the amount of time it takes to deploy the image. What should you recommend? (Choose all that apply.)
A. Create a new automatic deployment rule.
B. Synchronize software updates before deploying the image.
C. Upgrade the image from Windows 7 to Windows 7 Service Pack 1 (SP1).
D. Add an additional Install Software Updates step to the deployment task sequence.
E. Use offline servicing for the image.
Answer: CE
Explanation:
E:
* Offline Servicing: This new capability lets you schedule ConfigMgr to apply updates to an OS image imported into ConfigMgr without actually deploying the image. This potentially removes the need to deploy updates during an image capture or deployment, greatly reducing the time and effort spent on them and ensuring that operating systems deployed by ConfigMgr are fully updated before brought online.
* Whether you use a Build and Capture task sequence to automatically build your images or manually build your images, a great new feature of ConfigMgr 2012 is the ability to install updates directly into an image contained in a WIM file. This functionality isn’t actually new as it has existed in the stand-alone DISM tool from the beginning, but incorporating it directly into the ConfigMgr console makes it more accessible, enables it to leverage the software updates functionality of ConfigMgr itself, and makes it schedulable.
QUESTION 74
Your network contains a System Center 2012 Configuration Manage environment. The environment contains a primary site server named Server1 and a server named Server2 that runs Microsoft SQL Server 2008 R2. Server2 contains the Configuration Manager database. Server2 fails. You install SQL Server 2008 R2 on a new server. You name the server Server3. You need to restore the Configuration Manager database to Server3. What should you do?
A. Register the Service Principal Name (SPN) for the SQL Server service account of Server3.
From Server1, run the Configuration Manager 2012 Setup Wizard.
B. From Server3, run Microsoft SQL Server Management Studio, and then restore the backed up SQL Server database and log files.
C. From Server3, run Microsoft SQL Server Management Studio, and then attach the backed up SQL Server database and log files.
D. Register the Service Principal Name (SPN) for the SQL Server service account of Server3.
From Server1, run the Site Repair Wizard.
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/gg712697.aspx
Backup and Recovery in Configuration Manager.
Recover a Configuration Manager Site.
A Configuration Manager site recovery is required whenever a Configuration Manager site fails or data loss occurs in the site database. Repairing and resynchronizing data are the core tasks of a site recovery and are required to prevent interruption of operations. Site recovery is started by running the Configuration Manager Setup Wizard from installation media or by configuring the unattended installation script and then using the Setup command /script option. Your recovery options vary depending on whether you have a backup of the Configuration Manager site database.
Site Database Recovery Options.
When you run Setup, you have the following recovery options for the site database:
* Recover the site database using a backup set: Use this option when you have a backup of the Configuration Manager site database that was created as part of the Backup Site Server maintenance task run on the site before the site database failure. When you have a hierarchy, the changes that were made to the site database after the last site database backup are retrieved from the central administration site for a primary site, or from a reference primary site for a central administration site. When you recover the site database for a stand-alone primary site, you lose site changes after the last backup. When you recover the site database for a site in a hierarchy, the recovery behavior is different for a central administration site and primary site, and when the last backup is inside or outside of the SQL Server change tracking retention period.
Further information:
SCCM 2007 needed you to run Site Repair Wizard.
QUESTION 75
Your network contains a single Active Directory forest. You plan to deploy System Center 2012 Configuration Manager. The hierarchy will have a Central Administration site and two primary sites. You need to ensure that you can target user groups for application deployment. The solution must minimize network traffic. Which Configuration Manager discovery methods should you use?
A. Active Directory User Discovery on every site
B. Active Directory User Discovery and Active Directory Group Discovery on the primary sites
C. Active Directory User Discovery and Active Directory Group Discovery on the Central Administration site
D. Active Directory User Discovery on the primary sites and Active Directory Group Discovery on the Central Administration site
Answer: B
Explanation:
You can configure discovery operations throughout the hierarchy from the central administration site by assigning discovery methods to run at individual sites.
http://technet.microsoft.com/en-us/library/64aa34e1-c465-4eb8-820b-5c1702ab55ae#Plan_Where_to_Install_Sites
Note:
* Active Directory User Discovery. Discovers user accounts from the specified locations in Active Directory Domain Services.
* Active Directory Group Discovery. Discovers local, global, and universal security groups, the membership within these groups, and the membership within distribution groups from the specified locations in Active directory Domain Services. Distribution groups are not discovered as group resources.
Get the newest PassLeader 70-243 VCE dumps here: http://www.passleader.com/70-243.html (185 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-243 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpfmVaZDlXWUtVTTZVWWQ1Z3ZHdk1Gb0pBbWN4V2VOclZqcnFaUk5udTRUeGc