Valid 70-243 Dumps shared by PassLeader for Helping Passing 70-243 Exam! PassLeader now offer the newest 70-243 VCE dumps and 70-243 PDF dumps, the PassLeader 70-243 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-243 dumps with VCE and PDF here: http://www.passleader.com/70-243.html (185 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-243 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpfmVaZDlXWUtVTTZVWWQ1Z3ZHdk1Gb0pBbWN4V2VOclZqcnFaUk5udTRUeGc
QUESTION 91
You have a System Center 2012 Configuration Manager environment. You are deploying operating systems and migrating user profiles. You configure the state migration point to immediately delete profile data. Migrations are failing for user profiles that are larger than 25 GB. You need to successfully migrate all user profiles. What should you do?
A. Increase the retention period on the state migration point deletion policy.
B. Decrease the minimum free space size setting on the state migration point.
C. Remove unnecessary applications from the computers that are being migrated.
D. Increase the hard disk space on the computers that are being migrated.
Answer: B
QUESTION 92
You have a System Center 2012 Configuration Manager environment. During an operating system deployment to a specific computer, you need to ensure that all user state data is migrated to a new computer. What should you do?
A. Configure a user state restore task, and configure the task to transfer the data to the new computer.
B. Configure a user state restore task, and select the Customize how user profiles are restored option.
C. Create a computer association, and specify the details for the transfer.
D. Edit the MigSys.xml file that is specified in the user state restore task.
Answer: C
QUESTION 93
You install System Center 2012 Configuration Manager in your Active Directory environment. You configure a single Configuration Manager site. You need to enable Network Access Protection in your environment. You extend the Active Directory schema. You create the System Management container in Active Directory. You set permissions on the System Management container for the site server. Which three actions should you perform next? (Each correct answer presents part of the solution. Choose three.)
A. Enable the Network Access Protection client agent.
B. Enable the Software Updates client agent.
C. Configure the Configuration Manager site to publish settings to Active Directory.
D. Configure the Configuration Manager site for native mode.
E. Enable the Desired Configuration Management client agent.
F. Configure a server with the system health validator point and the Network Policy Server role.
Answer: ACF
QUESTION 94
You have a System Center 2012 Configuration Manager environment. You use System Center Operations Manager 2007 to monitor your Configuration Manager 2007 servers. You need to generate an alert when a software distribution point fails. What should you monitor?
A. the ccmexec.log file
B. component status of your distribution points
C. site system status of your distribution points
D. the smsprov.log file
Answer: C
QUESTION 95
You have a System Center 2012 Configuration Manager environment. When users attempt to install a program by using the Run Advertise program, they receive a message that the desired software is not available. You need to view the status to find out why software is not available. What should you do?
A. Connect to the client computers, and view the LocationServices.log file.
B. Connect to the client computers, and view the DataTransferService.log file.
C. Connect to the distribution point, and view the LocationServices.log file.
D. Connect to the distribution point, and view the PatchDownloader.log file.
Answer: A
QUESTION 96
You have a System Center 2012 Configuration Manager environment. You apply a desired configuration baseline named Baseline1 to all servers in a collection named Coll1. You need to view Baseline1 configuration results. What should you do?
A. Create a new Web report based on status message.
B. Create a new Web report based on hardware inventory.
C. Run an Asset Intelligence Web report for Coll1.
D. Run a compliance summary Web report for Coll1.
Answer: D
QUESTION 97
You have a System Center 2012 Configuration Manager environment. You need to prevent computers in remote offices from installing packages from the distribution point in the main office. What should you do?
A. Configure the central site system role with protected boundaries.
B. Configure the remote office site system roles with protected boundaries.
C. Configure the central site distribution point as a protected distribution point.
D. Configure the remote office distribution points as protected distribution points.
Answer: A
QUESTION 98
Your network contains a System center 2012 Configuration Manager environment. The environment contains a reporting services point. A group of users is responsible for creating custom reports. The custom reports will be published. You need to identify which tools can be used to create and publish custom reports to Microsoft SQL Server Reporting Services (SSRS). Which tools should you identify? (Choose all that apply.)
A. Report Builder
B. Microsoft SQL Server Business Intelligence Development Studio
C. Microsoft Access 2010
D. Reporting Services Configuration Manager
E. Microsoft SQL Server Management Studio
Answer: AB
Explanation:
A:
* Report Builder. ConfigMgr uses Report Builder 2.0 for authoring reports.
* Report Builder 1.0 first shipped with SQL Server 2005. Since then there have been two major upgrades, with Report Builder 3.0 emerging as the latest and the required version for SQL Server 2008 R2.
B:
Create a Report SQL Statement in SQL Server Business Intelligence Development Studio and Create a New Configuration Manager Report.
QUESTION 99
Your network contains a System center 2012 Configuration Manager environment. You are creating a configuration item that contains application settings for Microsoft Office 2010. You need to detect whether Office 2010 is installed before validating the configuration item. What should you do?
A. Create a report to display all installed software.
B. Enable Use a custom script to detect this application.
C. Create a direct membership collection.
D. Create an automatic deployment rule.
Answer: B
Explanation:
Create Configuration Item Wizard.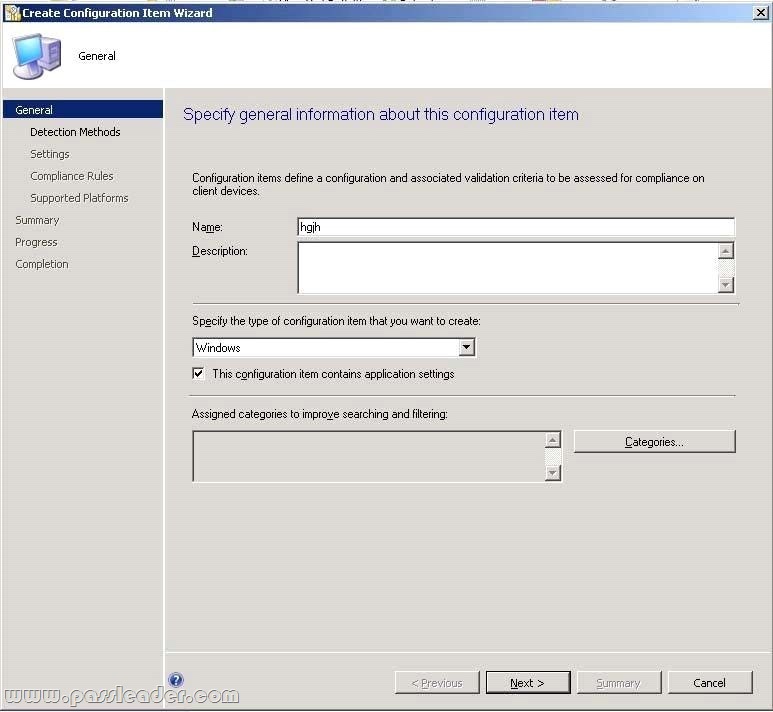

QUESTION 100
Your network contains a System Center 2012 Configuration Manager environment. You create a report named Report1. Report1 is used by multiple users. Users report that it takes too long to load Report1. You need to reduce the amount of time it takes to load Report1. What should you do?
A. Enable caching for the report.
B. Decrease the Size of the ReportServer database.
C. Decrease the session timeout value for the Reports website.
D. Increase the size of the ReportServerTempDB database.
Answer: A
Explanation:
Report caching can shorten the time it takes for a user to retrieve a report, particularly if the report is large or accessed frequently. When a report is requested, a query is sent to the database, an intermediate form of the report is cached on the report server, and the final report is rendered to the end user. Report caching forces the intermediate version of the report to be cached on the report server and provides a more consistent user experience with a reduced load on the database.
QUESTION 101
Your network contains a System Center 2012 Configuration Manager environment. Two weeks ago, you deployed a Windows Installer package named App1. You need to remediate a registry value that applies only to the client computers that have App1 installed. The solution must minimize network traffic. What should you do?
A. Modify the App1 Windows Installer package to contain the registry setting, and then create a new application for Appl.
B. Modify the App1 Windows Installer package to contain the registry setting, and then configure the existing application for App1 to use the new Windows Installer package.
C. Create an application-based configuration item, configure a rule for an existential type, and then import the registry setting from a client computer that has App1 installed.
D. Create an application-based configuration item, configure the detection method to use the Windows Installer product code of App1, and then import the registry setting from a client computer that has App1 installed.
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/gg682139.aspx
Introduction to Compliance Settings in Configuration Manager.
Compliance settings in System Center 2012 Configuration Manager provides a unified interface and user experience that lets you manage the configuration and compliance of servers, laptops, desktop computers, and mobile devices in your organization. Compliance settings contains tools to help you assess the compliance of users and client devices for many configurations, such as whether the correct Windows operating system versions are installed and configured appropriately, whether all required applications are installed and configured correctly, whether optional applications are configured appropriately, and whether prohibited applications are installed. Additionally, you can check for compliance with software updates, security settings, and mobile devices. Configuration item settings of the type Windows Management Instrumentation (WMI), registry, script, and all mobile device settings in Configuration Manager let you automatically remediate noncompliant settings when they are found. Compliance is evaluated by defining a configuration baseline that contains the configuration items that you want to evaluate and settings and rules that describe the level of compliance you must have. You can import this configuration data from the web in Microsoft System Center Configuration Manager Configuration Packs as best practices that are defined by Microsoft and other vendors, in Configuration Manager, and that you then import into Configuration Manager. Or, an administrative user can create new configuration items and configuration baselines.
http://technet.microsoft.com/en-us/library/gg712331.aspx
How to Create Windows Configuration Items for Compliance Settings in Configuration Manager.
Create configuration items in System Center 2012 Configuration Manager to define configurations that you want to manage and assess for compliance on devices. There are different types of configuration items:
1. Application configuration item:
Used to determine compliance for an application. This can include whether the application is installed and details about its configuration.
2. Operating system configuration item:
Used to determine compliance for settings that relate to the operating system and its configuration.
3. Software updates configuration item:
Automatically created when you download software updates with Configuration Manager. You do not create or see these configuration items in the Compliance Settings node, but you can select them when you define configuration baselines.
4. General configuration item:
Used to determine compliance for mobile devices.
Steps to Create a New Configuration Item for Client Computers.
Use the following required steps to create a configuration item by using the Create Configuration Item Wizard:
Step 1: Start the Create Configuration Item Wizard.
Step 2: Provide general information about the configuration item.
Step 3: Provide detection method information for the configuration item.
Step 4: Configure settings for the configuration item.
Step 5: Configure compliance rules for the configuration item.
Step 6: Specify supported platforms for the configuration item.
Step 7: Complete the wizard.
Further information:
http://technet.microsoft.com/en-us/library/gg712331.aspx#BKMK_Step3
Step 3: Provide Detection Method Information for the Configuration Item.
Use this procedure to provide detection method information for the configuration item. Note: Applies only if you selected This configuration item contains application settings on the General page of the wizard. A detection method in Configuration Manager contains rules that are used to detect whether an application is installed on a computer. This detection occurs before the configuration item is assessed for compliance. To detect whether an application is installed, you can detect the presence of a Windows Installer file for the application, use a custom script, or select Always assume application is installed to assess the configuration item for compliance regardless of whether the application is installed.
QUESTION 102
Your company has a production network and a test network. Both networks have System Center 2012 Configuration Manager deployed. You create the following objects on the test network:
– A configuration item named WebCI.
– A configuration baseline named WebBaseline that contains WebCI.
– A collection named WebServers that contains all of the Web servers on the test network.
You export the configuration baseline to Baseline.cab. You open the Configuration Manager console, you click Assets and Compliance, and then you expand Compliance Settings. You need to apply the configuration baseline to the Web servers on the production network. What should you do next? (Choose all that apply.)
A. Right-click WebBaseline, select Categorize, and then select Server.
B. Right-click Configuration Baselines, and then select Import Configuration Data.
C. Right-click WebCI, select Export, and then specify Baseline.cab as the export file.
D. Right-click WebBaseline, and then select Properties. In the Deployments tab, type WebServers in the Filter box.
E. Right-click WebBaseline, select Deploy, and then select the WebServers collection.
Answer: BE
Explanation:
Select Base line, deploy.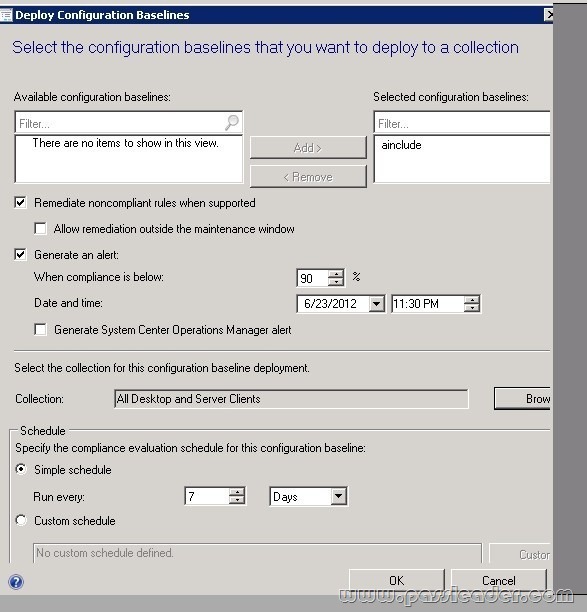
QUESTION 103
Your company uses System Center 2012 Configuration Manager to monitor compliance. The company has a configuration baseline for each server that has the Web Server (IIS) server rote installed. A new corporate policy specifies that the maximum TCP window size for all of the Web servers must be 131,072 bytes. You discover that the TCP window size is set in the following registry entry:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\HTTP\Parameters\MaxBytesPerSecond
You need to generate an error message for all of the Web servers that do NOT comply with the corporate policy. What should you do?
A. Add a new configuration item that has a registry value setting type to the configuration baseline.
B. Create a query-based collection that contains all of the Web servers, and then initiate an inventory collection.
C. Create a query that returns a list of all the Web servers, and then search the query results for the registry value.
D. Add a new configuration item that has an Internet Information Services (IIS) metabase setting type to the configuration baseline.
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/gg682139.aspx
Introduction to Compliance Settings in Configuration Manager.
http://technet.microsoft.com/en-us/library/gg712331.aspx
How to Create Windows Configuration Items for Compliance Settings in Configuration Manager.
QUESTION 104
You have a System Center 2012 R2 Configuration Manager Service Pack 1 (SP1) deployment. You plan to create a Configuration Manager query. You need to identify which components can be included in the WQL statement. Which three components should you identify? Each correct answer presents a complete solution.
A. Criteria
B. Collection limiting
C. Security
D. Omit duplicate rows
E. Joins
Answer: ADE
QUESTION 105
You have a System Center 2012 R2 Configuration Manager Service Pack 1 (SP1) deployment. Hardware inventory is enabled for all of the Configuration Manager clients. You create a device collection named Finance. All of the client computers in the finance department are members of the Finance collection. You need to include Trusted Platform Module (TPM) information in the hardware inventory of the finance department computers. Which object should you configure in Configuration Manager?
A. Hardware Requirements
B. Custom Client Device Settings
C. Network Discovery
D. a configuration item
E. a computer association
Answer: D
Explanation:
We are going to use Desired Configuration Management to run a script on target machines. The script will run on a regular schedule and place Bitlocker data into a new WMI class named SCCM_Bitlocker. Then, we will SCCM extend hardware inventory so that it collects data from this new class.
Compliance Rules Setting.
First, we will need to create a configuration baseline, a configuration item and two compliance rules.
Reference: Tracking Bitlocker Status using SCCM 2012.
https://winventures.wordpress.com/2013/09/18/tracking-bitlocker-status-using-sccm-2012/
Get the newest PassLeader 70-243 VCE dumps here: http://www.passleader.com/70-243.html (185 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-243 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpfmVaZDlXWUtVTTZVWWQ1Z3ZHdk1Gb0pBbWN4V2VOclZqcnFaUk5udTRUeGc