Valid 70-697 Dumps shared by PassLeader for Helping Passing 70-697 Exam! PassLeader now offer the newest 70-697 VCE dumps and 70-697 PDF dumps, the PassLeader 70-697 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-697 dumps with VCE and PDF here: http://www.passleader.com/70-697.html (201 Q&As Dumps –> 308 Q&As Dumps –> 350 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-697 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpd0pjaGx0bzVXVG8
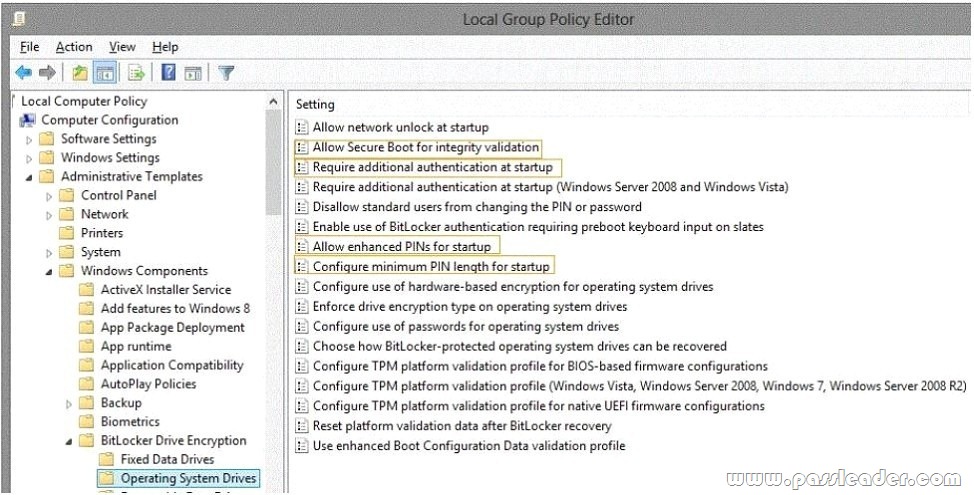
QUESTION 106
Hotspot Question
You administer Windows 10 Enterprise computers in your company network. All computers include Windows 10 Enterprise compatible Trusted Platform Module (TPM). You configure a computer that will run a credit card processing application. You need to ensure that the computer requires a user to enter a PIN code when starting the computer. Which policy should you configure? (To answer, select the appropriate policy in the answer area.)
QUESTION 107
Note: This question is part of a series of questions that use the same or similar answer choices. An answer choice may be correct for more than one question in the series. Each question is independent of the other questions in this series. Information and details provided in a question apply only to that question. You have a computer that runs Windows 10 and is used by 10 users. The computer is joined to an Active Directory domain. All of the users are members of the Administrators group. Each user has an Active Directory account. You have a Microsoft Word document that contains confidential information. You need to ensure that you are the only user who can open the document. What should you configure?
A. account policies
B. application control polices
C. HomeGroup settings
D. software restriction policies
E. NTFS permissions
F. Microsoft OneDrive
G. share permissions
H. Encrypting File System (EFS) settings
Answer: H
QUESTION 108
Hotspot Question
You plan to deploy a Microsoft Azure RemoteApp hybrid collection. You plan to use a custom template image named lmage1 to deploy the hybrid collection. You need to identify the role and feature that must be enabled in the image to support the deployment of the hybrid collection. What should you identify? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.
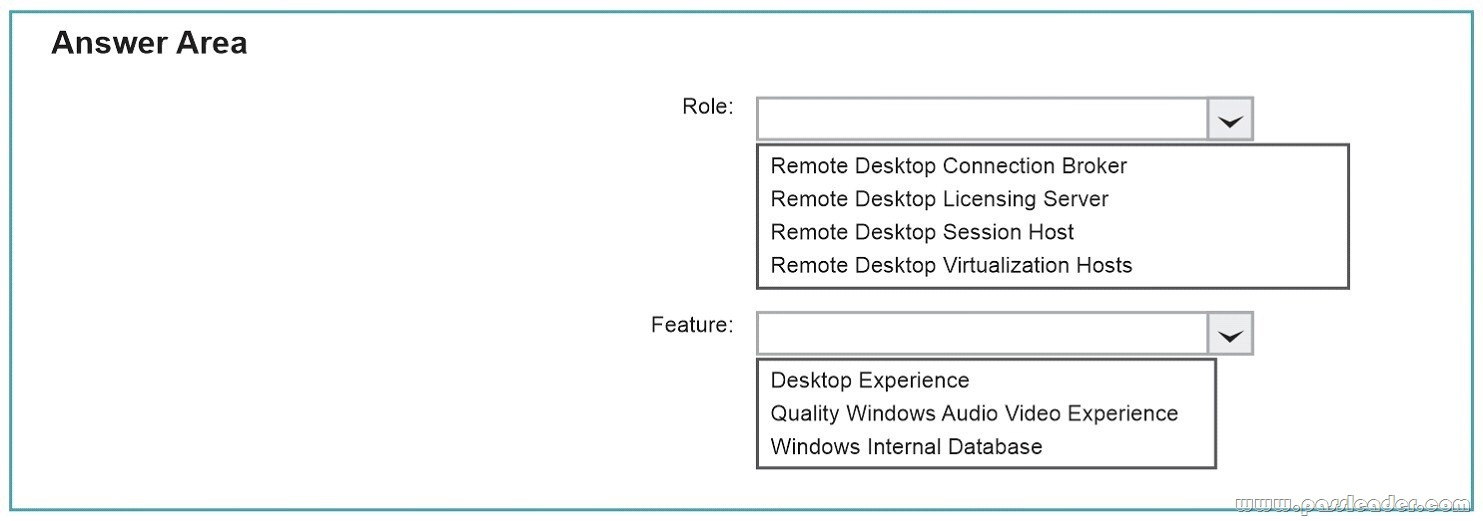
Answer:
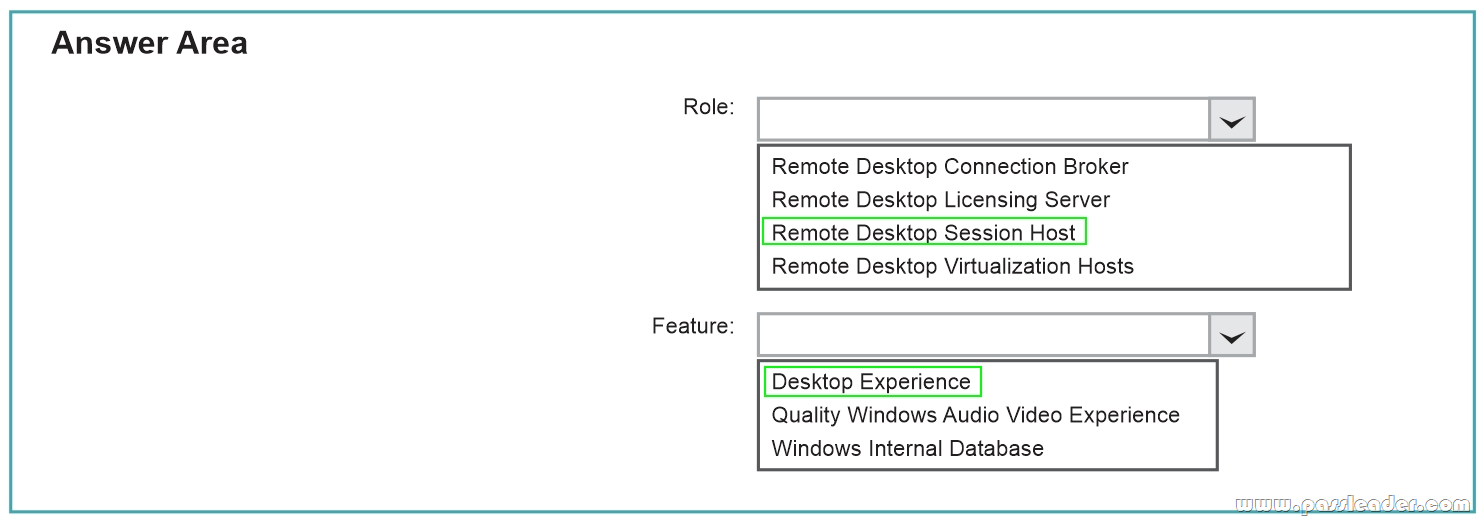
Explanation:
Link a template image. Azure RemoteApp uses a Windows Server 2012 R2 template image to host all the programs that you want to share with your users. To create a custom RemoteApp template image, you can start with an existing image or create a new one. I created a new one. The requirements for the image that can be uploaded for use with Azure RemoteApp are:
– It must be on a VHD file (VHDX files are not currently supported). The VHD can be either fixed-size or dynamically expanding. A dynamically expanding VHD is recommended because it takes less time to upload to Azure than a fixed-size VHD file.
– The disk must be initialized using the Master Boot Record (MBR) partitioning style. The GUID partition table (GPT) partition style is not supported. The VHD must contain a single installation of Windows Server 2012 R2. It can contain multiple volumes, but only one that contains an installation of Windows. The Remote Desktop Session Host (RDSH) role and the Desktop Experience feature must be installed.
– The Encrypting File System (EFS) must be disabled. The image must be SYSPREPed using the parameters /oobe /generalize /shutdown (DO NOT use the /mode:vm parameter).
QUESTION 109
Drag and Drop Question
You have a line-of-business universal app named Appl. You have an image of Windows 10 Enterprise named Image1. Image1 is mounted to the C:\Folder1 folder on a Windows 10 Enterprise computer named Computer1. The source for App1 is in the C:\folder2 folder. You need to ensure that App1 is included in Image1. What command should you run on Computer1? To answer, drag the appropriate values to the correct locations. Each value may be used once, more than once or not at all. You may need to drag the split bar between panes or scroll to view content.

Answer:

Explanation:
https://technet.microsoft.com/en-us/library/dn376490.aspx
QUESTION 110
You have a Microsoft Intune subscription. You need to uninstall the Intune agent from a computer. What should you do?
A. From the Groups node in the Microsoft Intune administration portal, click Delete.
B. From the computer run the provisioningutil.exe command.
C. From the computer, run the cltui.exe command.
D. From the computer use Programs and Features in Control Panel.
Answer: B
QUESTION 111
A company has 100 client computers that run Windows 8.1. The client computers are members of a workgroup. A custom application requires a Windows Firewall exception on each client computer. You need to configure the exception on the client computers without affecting existing firewall settings. Which Windows PowerShell cmdlet should you run on each client computer?
A. New-NetFirewallRule
B. Set-NetFirewallSetting
C. Set-NetFirewallRule
D. Set-NetFirewallProfile
E. New-NetIPSecMainModeRule
Answer: A
Explanation:
http://technet.microsoft.com/en-us/library/jj554908.aspx
New-NetFirewallRule. The New-NetFirewallRule cmdlet creates an inbound or outbound firewall rule and adds the rule to the target computer.
Further information:
– Set-NetFirewallSetting
The Set-NetFirewallSetting cmdlet configures properties that apply to the firewall and IPsec settings, regardless of which network profile is currently in use. This cmdlet allows the administrator to specify global firewall behavior.
– Set-NetFirewallRule
The Set-NetFirewallRule cmdlet modifies existing firewall rule properties.
– Set-NetFirewallProfile
The Set-NetFirewallProfile cmdlet configures options for the profiles, including domain, public, and private, that are global, or associated with the input rules.
– New-NetIPSecMainModeRule
The New-NetIPsecMainModeRule cmdlet creates an IPsec main mode rule. A main mode rule contains a set of local and remote end points to determine the peers to which it applies. When an application on the local computer attempts to communicate with one of these specified remote hosts, the computer attempts to establish a security association (SA) with the remote server.
QUESTION 112
You create a VPN connection that has the VPN type set to Automatic. When attempting to establish a VPN connection, which VPN protocol will be used first?
A. PPTP
B. L2TP
C. SSTP
D. IKEv2
Answer: D
Explanation:
https://blogs.technet.microsoft.com/networking/2014/01/13/configuring-native-vpn-client-through-pc-settings/
QUESTION 113
Drag and Drop Question
You have a Microsoft Intune subscription. You need to identify devices based on the following requirements:
– Devices that are jailbroken or rooted.
– Devices that are remote wiped or deleted.
– Devices that have blacklisted applications instated.
Which type of report should you use for each requirement? To answer, drag the appropriate reports to the correct requirements. Each report may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.

Answer:
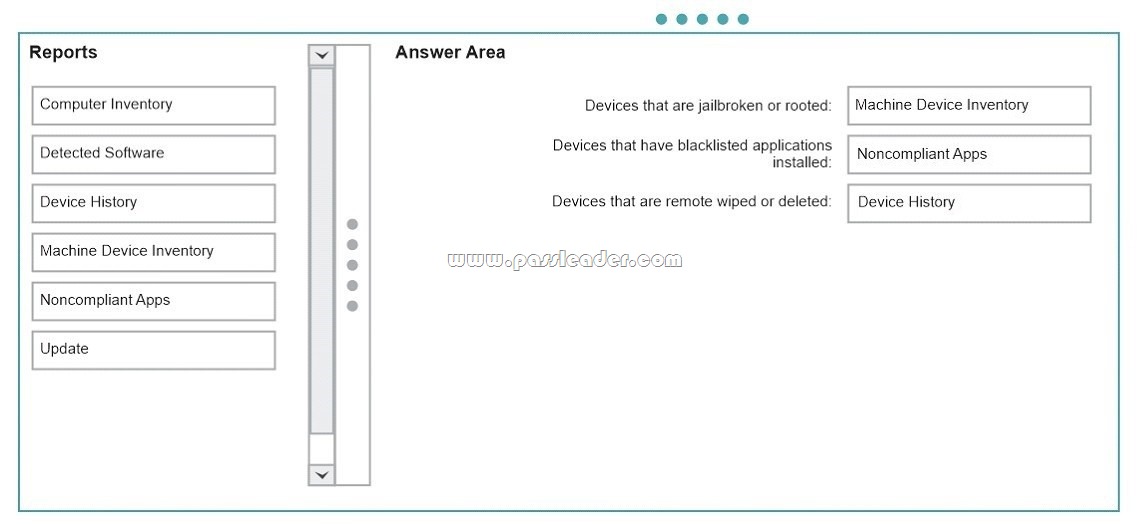
Explanation:
https://docs.microsoft.com/en-us/intune/deploy-use/understand-microsoft-intune-operations-by-using-reports
QUESTION 114
You have a computer that runs Windows 10. You install a second hard disk drive on the computer and you create a new volume named E. You need to enable system protection for volume E. What should you use?
A. the Wbadmin command
B. the Settings app
C. System Properties
D. the Set-Volume cmdlet
Answer: C
Explanation:
System protection is a feature that regularly creates and saves information about your computer’s system files and settings. System protection also saves previous versions of files that you’ve modified. It saves these files in restore points, which are created just before significant system events, such as the installation of a program or device driver. They’re also created automatically once every seven days if no other restore points were created in the previous seven days, but you can create restore points manually at any time.When system protection is turned on, you can undo undesired system changes by doing a system restore to revert your computer (all drives that have system protection turned on) to a previous point in time.This tutorial will show you how to turn on or off system protection for drives of your choice to be able to create restore points and do a system restore in Windows 10.You must be signed in as an administrator to be able to turn on or off system protection.
QUESTION 115
You manage a client Windows 10 Enterprise computer named Computer1. You have an OneDrive synchronized folder that contains .pdf files. You need to ensure that you can restore previous versions of the .pdf files. What should you do?
A. Enable File History.
B. Configure System Restore.
C. Configure Computer1 as a trusted PC.
D. Enable Sync your settings on Computer1.
Answer: A
Explanation:
File History regularly backs up versions of your files in the Documents, Music, Pictures, Videos, and Desktop folders and the OneDrive files available offline on your PC. Over time, you’ll have a complete history of your files. If the originals are lost, damaged, or deleted, you can restore them. You can also browse and restore different versions of your files. For example, if you want to restore an older version of a file (even if it wasn’t deleted or lost), you can browse through a timeline, select the version you want, and restore it.
QUESTION 116
A company has an Active Directory Domain Services (AD DS) domain with one physical domain controller. All client computers run Windows 10 Enterprise. A client computer hosts a Windows 10 Enterprise virtual machine (VM) test environment. The VMs are connected to a private virtual switch that is configured as shown in the Virtual Switch Manager exhibit. (Click the Exhibit button.)

You have the following requirements:
– Configure the test environment to allow VMs to communicate with the host machine.
– Minimize impact on the host machine.
You need to meet the requirements. What should you do?
A. Create a new virtual switch with a Private Network [CP1] connection type.
B. Create a new virtual switch with an ExternalNetwork connection type.
C. Change the VLAN ID of the private virtual switch to Enable Virtual LAN identification.
D. Create a new virtual switch with an Internal Network connection type.
Answer: D
Explanation:
http://john.bryntze.net/jbkb-v2/certification-exam-70-687-configuring-windows-8-part-2-configure-hardware-and-applications-16/
Virtual switches/ Hyper-V VLAN – you can create 3 different types of virtual switches depending the needs of your virtual machines and one single machine can use multiple virtual NICs that is member of different Virtual Switches.
External – This virtual switch binds to the physical network adapter and create a new adapter you can see in Control Panel\Network and Internet\Network Connections so if a virtual machine needs contact outside the host machine this one is a must.
Internal – This virtual switch can be used to connect all virtual machines and the host machine but cannot go outside that.
Private – This virtual switch can only be used by the virtual host.
Further information:
http://technet.microsoft.com/en-us/library/cc816585%28v=ws.10%29.aspx
Configuring Virtual Networks
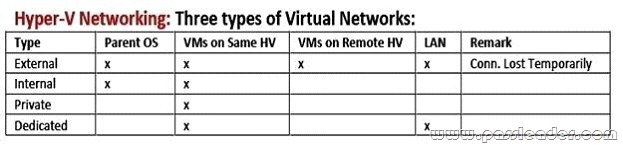
Private will not allow communication with the host machine. External will allow communication with the host machine but also allow access to other machines on the host machine’s network which is not a requirement.
QUESTION 117
Your network contains an Active Directory domain named contoso.local. All users have email addresses in the @contoso.com domain. You need to ensure that users can register Windows Phone 8.1 devices for mobile device management (MDM). Which DNS record should you create?
A. Enterprisedevice.contoso.com
B. Deviceregistration.contoso.local
C. Deviceregistration.contoso.com
D. Enterpriseregistration.contoso.com
E. Enterpriseregistration.contoso.local
Answer: D
Explanation:
https://technet.microsoft.com/en-us/windows/dn771709.aspx
QUESTION 118
A company has an Active Directory Domain Services (AD DS) domain. All client computers run Windows 10 Enterprise and are joined to the domain. You have the following requirements:
– Ensure that files in shared network folders are available offline.
– Maximize efficiency for users who connect to shared network folders from a mobile device.
You need to configure Group Policy settings to meet the requirements. What should you do first?
A. Enable the Enable file synchronization on costed networks policy setting.
B. Enable the Synchronize all offline files when logging on policy setting.
C. Enable and configure the Configure slow-link mode policy setting.
D. Enable and configure the Specify administratively assigned Offline Files policy setting.
Answer: A
Explanation:
https://technet.microsoft.com/en-us/library/hh968298.aspx
QUESTION 119
Hotspot Question
You have an Active Directory domain named contoso.com. You have a server that runs Windows Server 2012 R2 and that is a Remote Desktop server. The RD Web Access Web application settings are shown in the following graphic.

Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic. NOTE: Each correct selection is worth one point.

QUESTION 120
Note: This question is part of a series of questions that use the same or similar answer choices. An answer choice may be correct for more than one question in the series. Each question is independent of the other questions in this series. Information and details provided in a question apply only to that question. You have a computer that runs Windows 10 and is used by 10 users. The computer is joined to an Active Directory domain. Each user has an Active Directory account. You need to ensure that all of the users can access the files located in one another’s libraries. What should you configure?
A. Microsoft OneDrive
B. HomeGroup settings
C. Encrypting File System (EFS) settings
D. NTFS permissions
E. account policies
F. share permissions
G. software restriction policies
H. application control policies
Answer: D
Get the newest PassLeader 70-697 VCE dumps here: http://www.passleader.com/70-697.html (201 Q&As Dumps –> 308 Q&As Dumps –> 350 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-697 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpd0pjaGx0bzVXVG8

