Valid 70-534 Dumps shared by PassLeader for Helping Passing 70-534 Exam! PassLeader now offer the newest 70-534 VCE dumps and 70-534 PDF dumps, the PassLeader 70-534 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-534 dumps with VCE and PDF here: http://www.passleader.com/70-534.html (231 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-534 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpUUNnSVA5SFdpZ2c
QUESTION 101
An application sends Azure push notifications to a client application that runs on Windows Phone, iOS, and Android devices. Users cannot use the application on some devices. The authentication mechanisms that the application uses are the source of the problem. You need to monitor the number of notifications that failed because of authentication errors. Which three metrics should you monitor? Each correct answer presents part of the solution.
A. Microsoft Push Notification Service (MPNS) authentication errors
B. External notification system errors
C. Apple Push Notification Service (APNS) authentication errors
D. Channel errors
E. Windows Push Notification Services (WNS) authentication errors
F. Google Cloud Messaging (GCM) authentication errors
Answer: ACF
QUESTION 102
You administer an Azure Active Directory (Azure AD) tenant that has a SharePoint web application named TeamSite1. TeamSite1 accesses your Azure AD tenant for user information. The application access key for TeamSite1 has been compromised. You need to ensure that users can continue to use TeamSite1 and that the compromised key does not allow access to the data in your Azure AD tenant. Which two actions should you perform? Each correct answer presents part of the solution.
A. Remove the compromised key from the application definition for TeamSite1.
B. Delete the application definition for TeamSite1.
C. Generate a new application key for TeamSite1.
D. Generate a new application definition for TeamSite1.
E. Update the existing application key.
Answer: AC
Explanation:
One of the security aspects of Windows Azure storage is that all access is protected by access keys. It is possible to change the access keys (e.g. if the keys become compromised), and if changed, we’d need to update the application to have the new key.
QUESTION 103
You manage a cloud service on two instances. The service name is Service1 and the role name is ServiceRole1. Service1 has performance issues during heavy traffic periods. You need to increase the existing deployment of Service1 to three instances. Which Power Shell cmdlet should you use?
A. PS C:\>Set-AzureService -ServiceName “Service1” -Label “ServiceRole1′ -Description “Instance count=3”
B. PS C:\>Set-AzureRole -ServiceName “Service1” -Slot “Production” -RoleName “ServiceRole1” -Count 3
C. PS C:\>Add-AzureWebRole -Name ‘ServiceRole1″ -Instances 3
D. PS C:\> $instancecount = New-Object Hashtable$settings[‘INSTANCECOUNT=3] PS C:\> Set-AzureWebsite -AppSettings $instancecount ServiceRole1
Answer: B
Explanation:
https://docs.microsoft.com/en-us/powershell/servicemanagement/azure.service/v1.6.1/set-azurerole
QUESTION 104
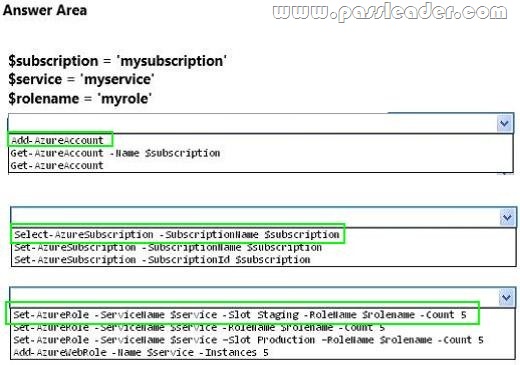
Hotspot Question
You deploy a new version of a cloud-service application to a staging slot. The application consists of one web role. You prepare to swap the new version of the application into the production slot. Your Azure account has access to multiple Azure subscriptions. You load the Azure PowerShell cmdlets into the Windows PowerShell command shell. The command shell is NOT configured for certificate-based authentication. You must use the Windows PowerShell command window to configure the application. You need to create five instances of the web role. How should you configure the relevant Windows PowerShell script? To answer, select the appropriate option or options in the answer area.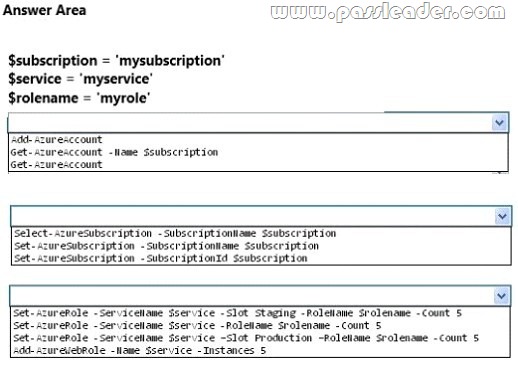
QUESTION 105
Your company has a subscription to Azure. You configure your contoso.com domain to use a private Certificate Authority. You deploy a web site named MyApp by using the Shared (Preview) web hosting plan. You need to ensure that clients are able to access the MyApp website by using https. What should you do?
A. Back up the Site and import into a new website.
B. Use the internal Certificate Authority and ensure that clients download the certificate chain.
C. Add custom domain SSL support to your current web hosting plan.
D. Change the web hosting plan to Standard.
Answer: D
Explanation:
Enabling HTTPS for a custom domain is only available for the Standard web hosting plan mode of Azure websites.
QUESTION 106
You manage a cloud service that hosts a customer-facing application. The application allows users to upload images and create collages. The cloud service is running in two medium instances and utilizes Azure Queue storage for image processing. The storage account is configured to be locally redundant. The sales department plans to send a newsletter to potential clients. As a result, you expect a significant increase in global traffic. You need to recommend a solution that meets the following requirements:
– Configure the cloud service to ensure the application is responsive to the traffic increase.
– Minimize hosting and administration costs.
What are two possible ways to achieve this goal? Each correct answer presents a complete solution.
A. Configure the cloud service to run in two Large instances.
B. Configure the cloud service to auto-scale to three instances when processor utilization is above 80%.
C. Configure the storage account to be geo-redundant.
D. Deploy a new cloud service in a separate data center.
Use Azure Traffic Manager to load balance traffic between the cloud services.
E. Configure the cloud service to auto-scale when the queue exceeds 1000 entries per machine.
Answer: BE
Explanation:
* An autoscaling solution reduces the amount of manual work involved in dynamically scaling an application. It can do this in two different ways: either preemptively by setting constraints on the number of role instances based on a timetable, or reactively by adjusting the number of role instances in response to some counter(s) or measurement(s) that you can collect from your application or from the Azure environment.
QUESTION 107
You manage an application running on Azure Web Sites Standard tier. The application uses a substantial amount of large image files and is used by people around the world. Users from Europe report that the load time of the site is slow. You need to implement a solution by using Azure services. Which two actions will achieve the goal? Each correct answer presents a complete solution.
A. Configure Azure blob storage with a custom domain.
B. Configure Azure CDN to cache all responses from the application web endpoint.
C. Configure Azure Web Site auto-scaling to increase instances at high load.
D. Configure Azure CDN to cache site images and content stored in Azure blob storage.
Answer: AD
Explanation:
Blobs that benefit the most from Azure CDN caching are those that are accessed frequently during their time-to-live (TTL) period. A blob stays in the cache for the TTL period and then is refreshed by the blob service after that time is elapsed. Then the process repeats.
http://azure.microsoft.com/en-us/documentation/articles/storage-custom-domainname/
http://blog.maartenballiauw.be/post/2013/08/20/Using-the-Windows-Azure-Content-Delivery-Network-CDN.aspx
QUESTION 108
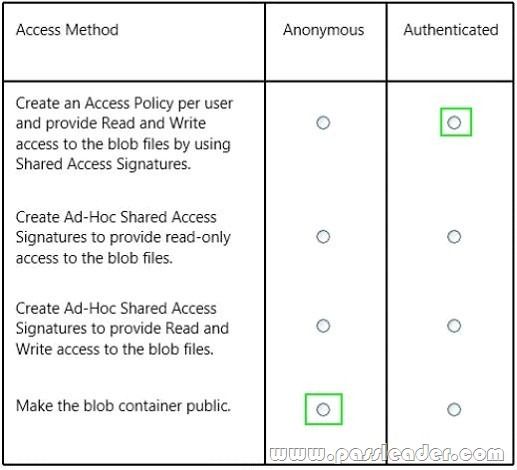
Hotspot Question
You manage a public-facing web application which allows authenticated users to upload and download large files. On the initial public page there is a promotional video. You plan to give users access to the site content and promotional video. In the table below, identify the access method that should be used for the anonymous and authenticated parts of the application. Make only one selection in each column.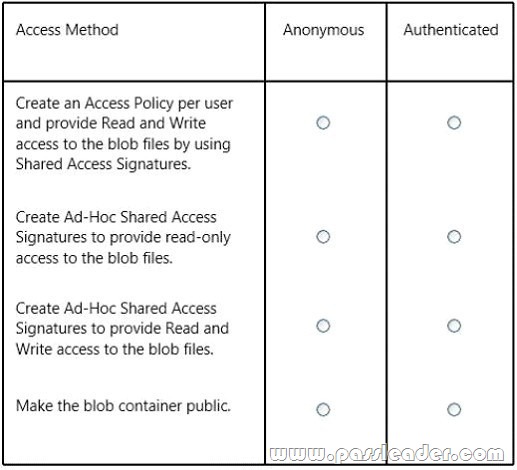
QUESTION 109
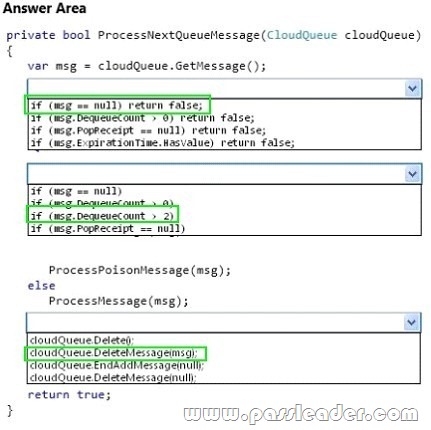
Hotspot Question
You are developing an Azure cloud service for a company. The cloud service monitors a queue for incoming messages and then processes invoices based on the contents of these messages. Some messages are formed incorrectly and cause exceptions. There is no time limit for how long the service takes to process an individual message. All messages must be processed at least once by using the ProcessMessage method. Messages must not be processed more than twice by using the ProcessMessage method. Messages that fail normal processing must be processed by using the ProcessPoisonMessage method. You need to configure message processing. How should you complete the relevant code? To answer, select the appropriate option or options in the answer area.
QUESTION 110
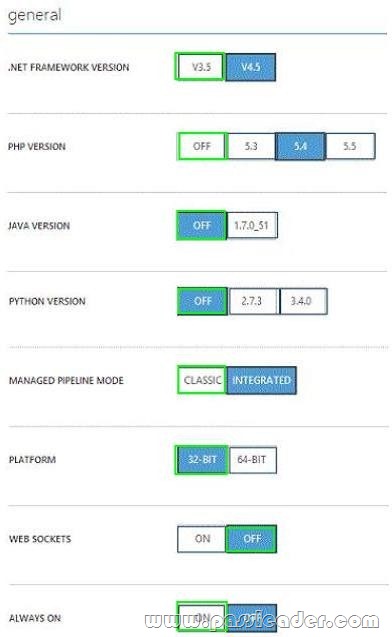
Hotspot Question
You manage an Internet Information Services (IIS) 6 website named contososite1. Contososite1 runs a legacy ASP.NET 1.1 application named LegacyApp1. LegacyApp1 does not contain any integration with any other systems or programming languages. You deploy contososite1 to Azure Web Sites. You need to configure Azure Web Sites. You have the following requirements:
– LegacyApp1 runs correctly.
– The application pool does not recycle.
Which settings should you configure to meet the requirements? To answer, select the appropriate settings in the answer area.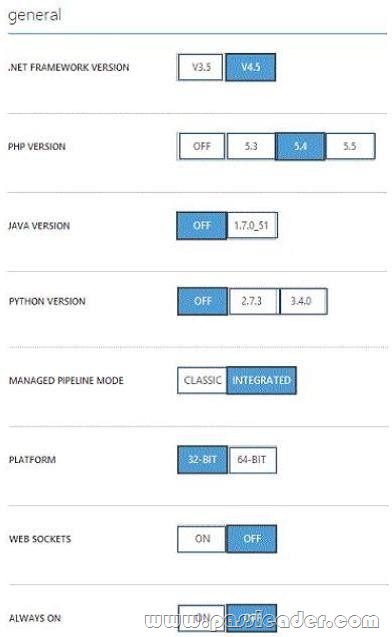
QUESTION 111
You plan to deploy an application as a cloud service. The application uses a virtual network to extend your on-premises network into Azure. You need to configure a site-to-site VPN for cross-premises network connections. Which two objects should you configure? Each correct answer presents part of the solution.
A. Dynamic routing gateway
B. VPN gateway
C. External-facing IPv6 address
D. External-facing IPv4 address
Answer: BD
QUESTION 112
Hotspot Question
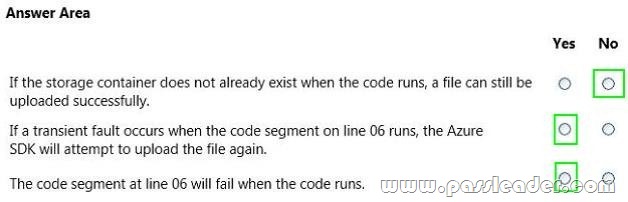
You have a WebJob object that runs as part of an Azure website. The WebJob object uses features from the Azure SDK for .NET. You use a well-formed but invalid storage key to create the storage account that you pass into the UploadDataToAzureStorage method. The WebJob object contains the following code segment. Line numbers are included for reference only.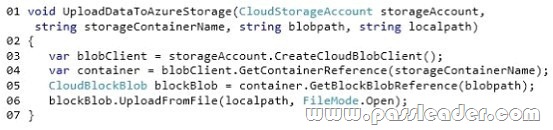
For each of the following statements, select Yes if the statement is true. Otherwise, select No.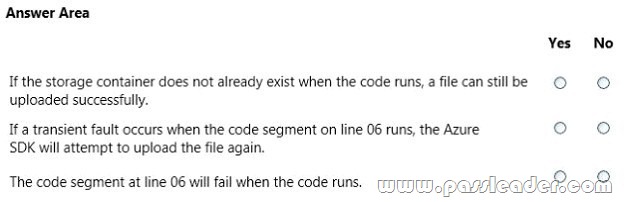
QUESTION 113
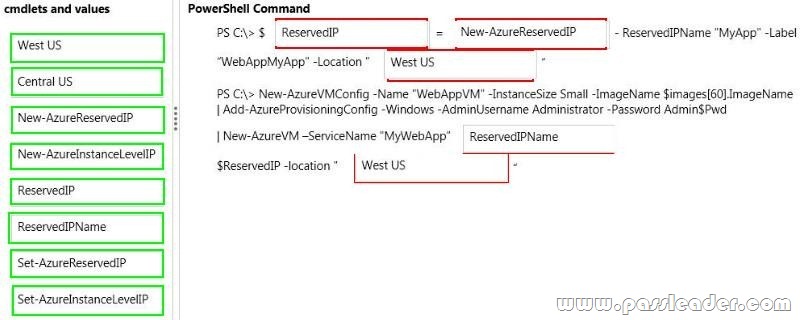
Drag and Drop Question
You administer an Azure Virtual Machine (VM) named CON-CL1. CON-CL1 is in a cloud service named ContosoService1. You want to create a new VM named MyApp that will have a fixed IP address and be hosted by an Azure Datacenter in the US West region. You need to assign a fixed IP address to the MyApp VM. Which Azure Power Shell cmdlets and values should you use? To answer, drag the appropriate cmdlet or value to the correct location in the PowerShell command. Each cmdlet or value may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.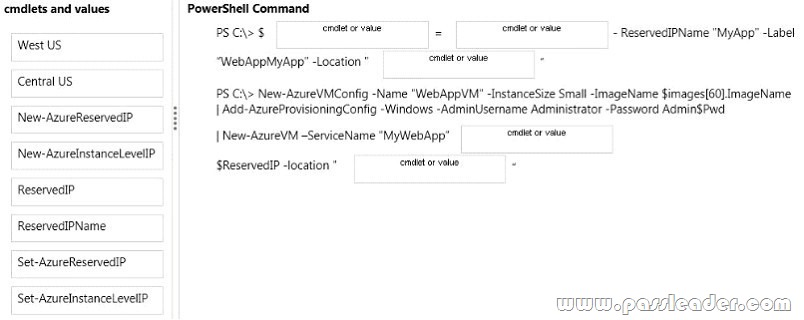
QUESTION 114
You manage an Azure subscription with virtual machines (VMs) that are running in Standard mode. You need to reduce the storage costs associated with the VMs. What should you do?
A. Locate and remove orphaned disks.
B. Add the VMs to an affinity group.
C. Change VMs to the Basic tier.
D. Delete the VHD container.
Answer: C
Explanation:
Standard offers 50 GB of storage space, while Basic only gives 10 GB but it will save costs.
http://azure.microsoft.com/en-us/pricing/details/websites/
QUESTION 115
You manage a web application published to Azure Cloud Services. Your service level agreement (SLA) requires that you are notified in the event of poor performance from customer locations in the US, Asia, and Europe. You need to configure the Azure Management Portal to notify you when the SLA performance targets are not met. What should you do?
A. Create an alert rule to monitor web endpoints.
B. Create a Notification Hub alert with response time metrics.
C. Add an endpoint monitor and alert rule to the Notification Hub.
D. Configure the performance counter on the cloud service.
Answer: A
Explanation:
* An alert rule enables you to monitor an available metric within a supported Azure service. When the value of a specified metric violates the threshold assigned for a rule, the alert rule becomes active and registers an alert. When you create an alert rule, you can select options to send an email notification to the service administrator and co- administrators, or another administrator, when the rule becomes active, and when an alert condition is resolved.
* You can configure cloud service alert rules on:
– Web endpoint status metrics
– Monitoring metrics from the cloud service host operating system Performance counters collected from the cloud service guest virtual machine
http://msdn.microsoft.com/en-us/library/azure/dn306639.aspx
QUESTION 116
Your company has recently signed up for Azure. You plan to register a Data Protection Manager (DPM) server with the Azure Backup service. You need to recommend a method for registering the DPM server with the Azure Backup vault. What are two possible ways to achieve this goal? Each correct answer presents a complete solution.
A. Import a self-signed certificate created using the makecert tool.
B. Import a self-signed certificate created using the createcert tool.
C. Import an X.509 v3 certificate with valid clientauthentication EKU.
D. Import an X.509 v3 certificate with valid serverauthentication EKU.
Answer: AC
Explanation:
A: You can create a self-signed certificate using the makecert tool, or use any valid SSL certificate issued by a Certification Authority (CA) trusted by Microsoft, whose root certificates are distributed via the Microsoft Root Certificate Program.
C: The certificate must have a valid ClientAuthentication EKU.
http://technet.microsoft.com/en-us/library/dn296608.aspx
QUESTION 117
Your company plans to migrate from On-Premises Exchange to Exchange Online in Office 365. You plan to integrate your existing Active Directory Domain Services (AD DS) infrastructure with Azure AD. You need to ensure that users can log in by using their existing AD DS accounts and passwords. You need to achieve this goal by using minimal additional systems. Which two actions should you perform? Each answer presents part of the solution.
A. Configure Password Sync.
B. Set up a DirSync Server.
C. Set up an Active Directory Federation Services Server.
D. Set up an Active Directory Federation Services Proxy Server.
Answer: BC
Explanation:
https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-dirsync-upgrade-get-started
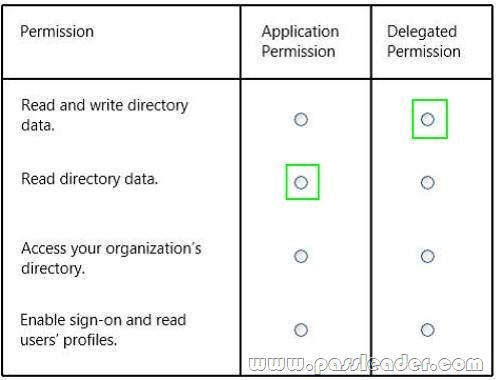
QUESTION 118
Hotspot Question
You administer an Azure Active Directory (Azure AD) tenant. You add a custom application to the tenant. The application must be able to:
– Read data from the tenant directly.
– Write data to the tenant on behalf of a user.
In the table below, identify the permission that must be granted to the application. Make only one selection in each column.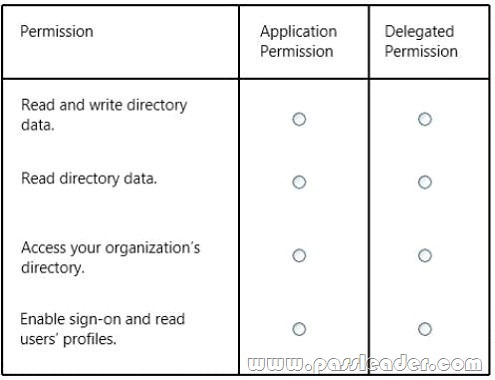
QUESTION 119
Drag and Drop Question
You deploy an application as a cloud service to Azure. The application contains a web role to convert temperatures between Celsius and Fahrenheit. The application does not correctly convert temperatures. You must use Microsoft Visual Studio to determine why the application does not correctly convert temperatures. You need to debug the source code in Azure. Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.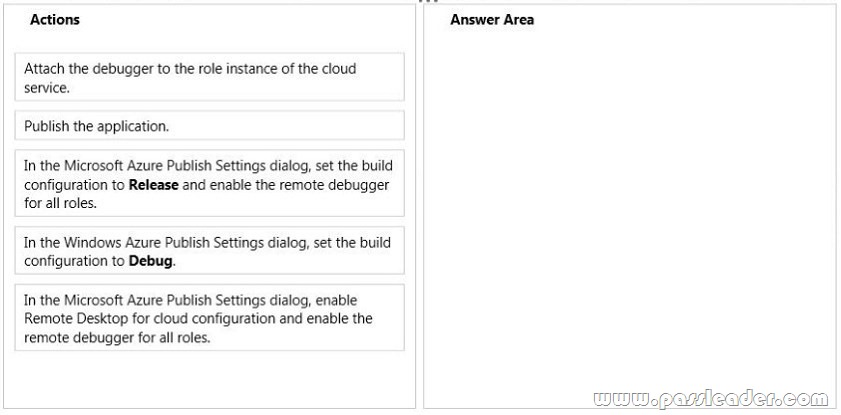
Answer: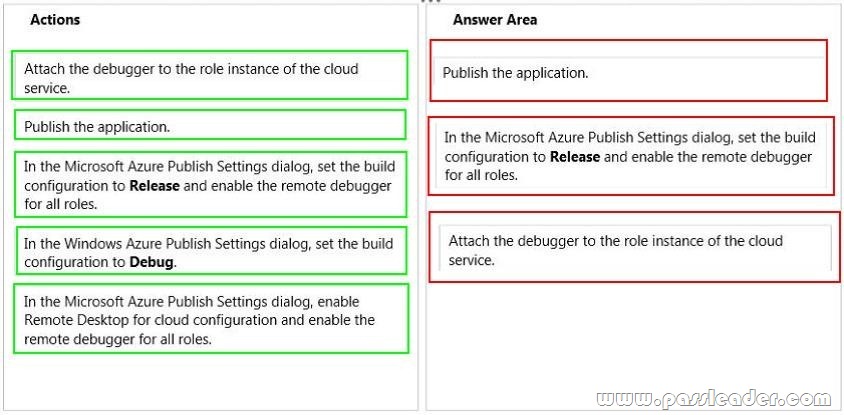
Explanation:
https://docs.microsoft.com/en-us/azure/vs-azure-tools-debug-cloud-services-virtual-machines
QUESTION 120
You develop a set of Power Shell scripts that will run when you deploy new virtual machines (VMs). You need to ensure that the scripts are executed on new VMs. You want to achieve this goal by using the least amount of administrative effort. What should you do?
A. Create a new GPO to execute the scripts as a logon script.
B. Create a SetupComplete.cmd batch file to call the scripts after the VM starts.
C. Create a new virtual hard disk (VHD) that contains the scripts.
D. Load the scripts to a common file share accessible by the VMs.
E. Set the VMs to execute a custom script extension.
Answer: E
Explanation:
After you deploy a Virtual Machine you typically need to make some changes before it’s ready to use. This is something you can do manually or you could use Remote PowerShell to automate the configuration of your VM after deployment for example. But now there’s a third alternative available allowing you customize your VM: the CustomScript extension. This CustomScript extension is executed by the VM Agent and it’s very straightforward: you specify which files it needs to download from your storage account and which file it needs to execute. You can even specify arguments that need to be passed to the script. The only requirement is that you execute a .ps1 file.
Get the newest PassLeader 70-534 VCE dumps here: http://www.passleader.com/70-534.html (231 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-534 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpUUNnSVA5SFdpZ2c