Valid 70-342 Dumps shared by PassLeader for Helping Passing 70-342 Exam! PassLeader now offer the newest 70-342 VCE dumps and 70-342 PDF dumps, the PassLeader 70-342 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-342 dumps with VCE and PDF here: http://www.passleader.com/70-342.html (233 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-342 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpfnExREVzWWtnTGZYZDhiVm1ESjV2dkgwU09EOExRMloxUE95aUdnWC1lUU0
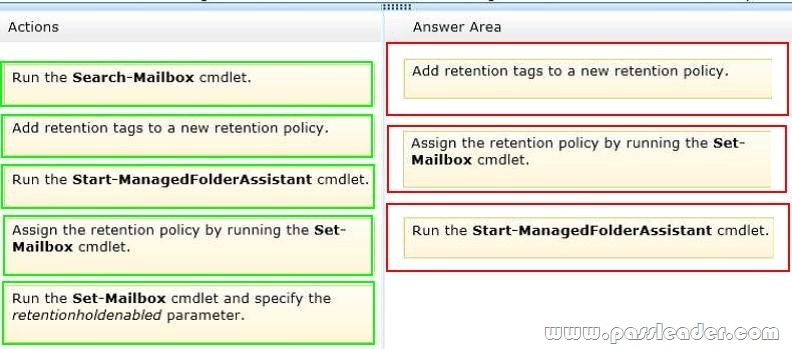
QUESTION 61
Drag and Drop Question
You have an Exchange Server organization named adatum.com. The organization contains servers that have Exchange Server 2010 and Exchange Server 2013 installed. The company executives require that all email messages remain stored for three years. You create two retention tags named Ret1 and Ret2. Ret1 moves the email messages to an Archive mailbox after one year. Ret2 permanently deletes the email messages after three years. You need to meet the company executives’ requirements. The solution must ensure that all email messages that are older than two years are removed as quickly as possible. Which three actions should you perform in sequence? (To answer, move the appropriate three actions from the list of actions to the answer area and arrange them in the correct order.)

QUESTION 62
You have an Exchange Server 2013 organization named adatum.com. The organization contains five Mailbox servers. You need to prevent a user named User8 from permanently deleting an email message in his mailbox. What should you do on the mailbox of User8?
A. Configure an in-place hold.
B. Create an Archive mailbox.
C. Configure a retention hold.
D. Create a Retention tag.
Answer: A
Explanation:
In Exchange 2013, you can use In-Place Hold to accomplish the following goals:
* Place user mailboxes on hold and preserve mailbox items immutably Preserve mailbox items deleted by users or automatic deletion processes such as MRM Use query-based In-Place Hold to search for and retain items matching specified criteria Preserve items indefinitely or for a specific duration Place a user on multiple holds for different cases or investigations Keep In-Place Hold transparent from the user by not having to suspend MRM Enable In-Place eDiscovery searches of items placed on hold.
Note:
When a reasonable expectation of litigation exists, organizations are required to preserve electronically stored information (ESI), including email that’s relevant to the case. This expectation often exists before the specifics of the case are known, and preservation is often broad. Organizations may need to preserve all email related to a specific topic or all email for certain individuals.
Failure to preserve email can expose an organization to legal and financial risks such as scrutiny of the organization’s records retention and discovery processes, adverse legal judgments, sanctions, or fines.
http://technet.microsoft.com/en-us/library/ff637980%28v=exchg.150%29.aspx
QUESTION 63
You have an Exchange Server 2013 organization named adatum.com. You have a database availability group (DAG) that contains four Exchange servers named Server1, Server2, Server3, and Server4. The file share witness is on a server named Share1. The organization has two Send connectors. The Send connectors are configured as shown in the following table.
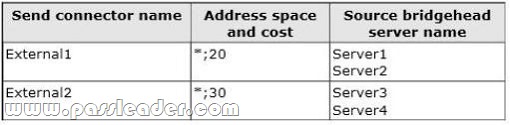
Users report that email sent to external recipients is not being received. You discover that outbound email messages are queued on Server3 and Server4. You need to ensure that all of the email messages queued on Server3 and Server4 are delivered to the Internet as quickly as possible. What should you do?
A. Modify the cost of External.
B. Disable External1.
C. Modify the list of source bridgehead servers of External2.
D. Modify the cost of External1.
Answer: B
Explanation:
Note:
* In Microsoft Exchange Server 2013, a Send connector controls the flow of outbound messages to the receiving server.
* When a message is to be delivered to a remote delivery group, a routing path must be determined for the message. Exchange 2013 uses the same logic as Exchange 2010 to select the routing path for a message:
– Calculate the least-cost routing path by adding the cost of the IP site links that must be traversed to reach the destination. If the destination is a connector, the cost assigned to the address space is added to the cost to reach the selected connector. If multiple routing paths are possible, the routing path with the lowest aggregate cost is used;
– If more than one routing path has the same cost, the routing path with the least number of hops is used;
– If more than one routing path is still available, the name assigned to the AD sites before the destination is considered. The routing path where the AD site nearest the destination is lowest in alphanumeric order is used. If the site nearest the destination is the same for all routing paths being evaluated, an earlier site name is considered.
http://social.technet.microsoft.com/Forums/exchange/en-US/3b89aecd-68c9-40d6-8573-eefb806e61f7/how-to-get-a-backup-send-connector-to-take-over?forum=exchange2010
QUESTION 64
You are a network administrator for a company named Humongous Insurance. Humongous Insurance has an Active Directory forest that contains two domains. You install the Active Directory Rights Management Services server role on a server named ADRMS1. The Active Directory Rights Management Services (AD RMS) server uses an internal certification authority (CA) for all certificates. You plan to provide users with the ability to use AD RMS to protect all of the email messages sent to a partner company named Contoso, Ltd. Contoso does not have AD RMS deployed. You need to identify which components from the Humongous Insurance network must be accessible to Contoso to ensure that the users at Contoso can open protected messages. Which two components should you identify? (Each correct answer presents part of the solution. Choose two.)
A. the AD RMS cluster
B. the certificate revocation list (CRL)
C. the Active Directory domain controllers
D. the Client Access servers
E. the Mailbox servers
F. the Global Catalog servers
Answer: BC
Explanation:
B:
The CRL is exactly what its name implies: a list of subscribers paired with digital certificate status. The list enumerates revoked certificates along with the reason(s) for revocation. The dates of certificate issue, and the entities that issued them, are also included. In addition, each list contains a proposed date for the next release. When a potential user attempts to access a server, the server allows or denies access based on the CRL entry for that particular user.
C:
If federation cannot be implemented and the external organization cannot implement their own AD RMS infrastructure, hosting the user accounts can be the best option. However, the cost of managing such accounts (for both the IT department and each user) must be considered. In this case, the users will need to be authenticated by a domain controller.
QUESTION 65
You have an Exchange Server organization that contains four servers. The servers are configured as shown in the following table.
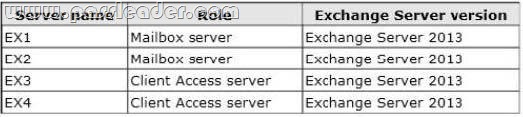
You are deploying Unified Messaging (UM). You create a dial plan named UMPIan1 and a UM mailbox policy named UMPlan Mailbox Policy. You need to ensure that all voice mail sent to the existing extension of a user is delivered to the user’s mailbox. Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.)
A. Create a UM hunt group.
B. Create a UM IP gateway.
C. Configure the IP-PBX to route calls to EX3 and EX4.
D. Configure the IP-PBX to route calls to EX1 and EX2.
E. Assign EX1 and EX2 to UMPIan1.
F. Assign EX3 and EX4 to UMPIan1.
Answer: ABC
Explanation:
Here are the basic steps for connecting VoIP gateways, IP PBXs, SIP-enabled PBXs, or SBCs to Client Access and Mailbox servers:
Step 1: Install the Client Access and Mailbox servers in your organization.
Step 2: Create and configure a Telephone Extension, SIP URI, or E.164 UM dial plan.
Step 3: Create and configure a UM IP gateway. You must create and configure a UM IP gateway for each VoIP gateway, IP PBX, SIP-enabled PBX, or SBC that will be accepting incoming calls and sending outgoing calls.
Step 4: Create a new UM hunt group if needed. If you create a UM IP gateway and don’t specify a UM dial plan, a UM hunt group will be automatically created.
QUESTION 66
Drag and Drop Question
You have an Exchange Server 2013 organization that contains two Mailbox servers and two Client Access servers. You have an Active Directory Rights Management Services (AD RMS) cluster. Information Rights Management (IRM) is enabled for the Exchange Server organization. All company executives are in a security group named Execs. All of the executives use smartphones that are managed by using a mobile device mailbox policy. The executives frequently read IRM-protected email messages by using Microsoft Outlook. You need to ensure that the executives can read the IRM-protected messages on their smartphone. Which task should you perform in each environment? (To answer, drag the appropriate tasks to the correct environments. Each task may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.)
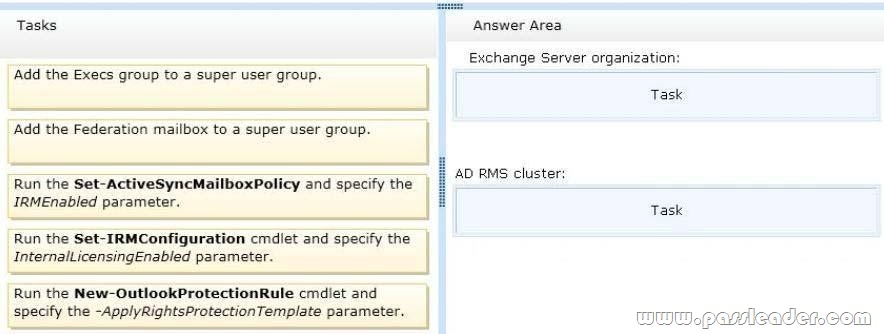
Answer:
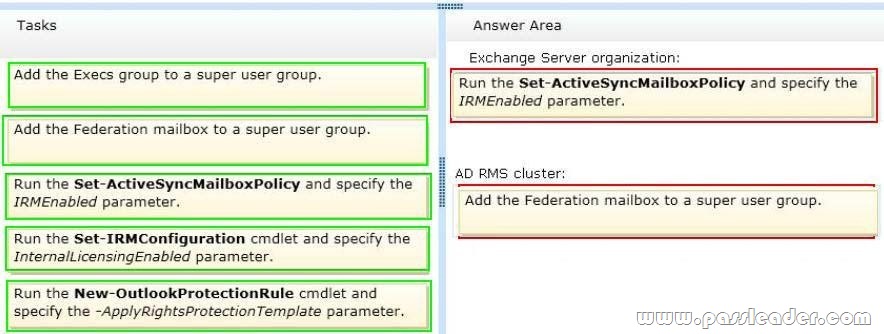
Explanation:
For the following Microsoft Exchange Server 2013 Information Rights Management (IRM) features to be enabled, you must add the Federation mailbox (a system mailbox created by Exchange 2013 Setup) to the super users group on your organization’s Active Directory Rights Management Services (AD RMS) cluster:
– IRM in Microsoft Office Outlook Web App
– IRM in Exchange ActiveSync
– Journal report decryption
– Transport decryption
The IrmEnabled parameter specifies whether Information Rights Management (IRM) is enabled for the mailbox policy.
QUESTION 67
Drag and Drop Question
Your company has two offices. Each office is configured as an Active Directory site. The sites are named Site1 and Site2. You have an Exchange Server 2013 organization that is configured as shown in the following exhibit. (Click the Exhibit button.)
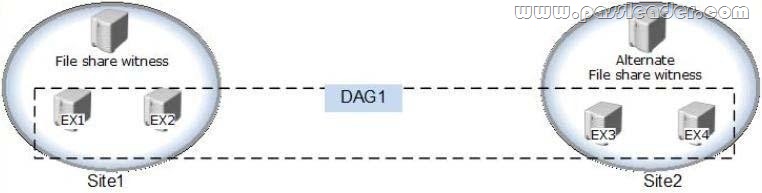
Datacenter Activation Coordination (DAC) mode is enabled on the database availability group (DAG) named DAG1. You are testing a site failover by shutting down all of the servers in Site1. You need to mount the databases in Site2. Which three commands should you run in sequence? (To answer, move the appropriate three commands from the list of commands to the answer area and arrange them in the correct order.)
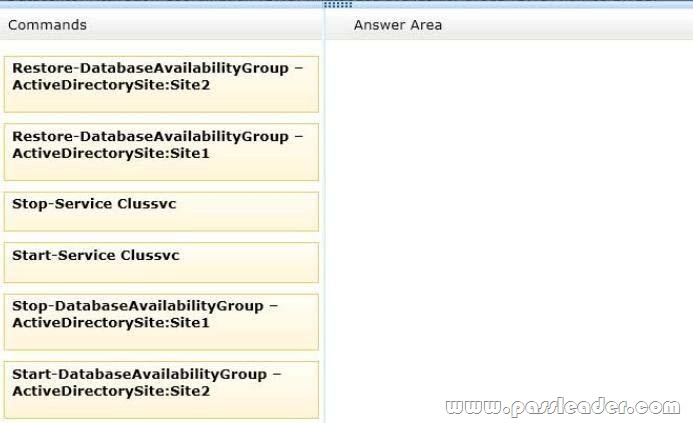
Answer:
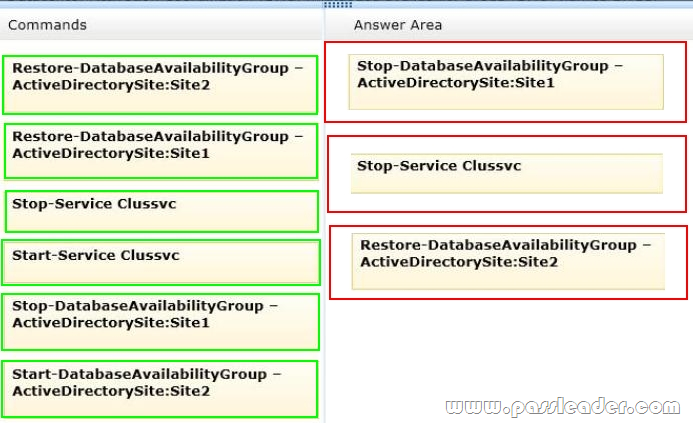
Explanation:
http://technet.microsoft.com/en-us/library/dd351049.aspx
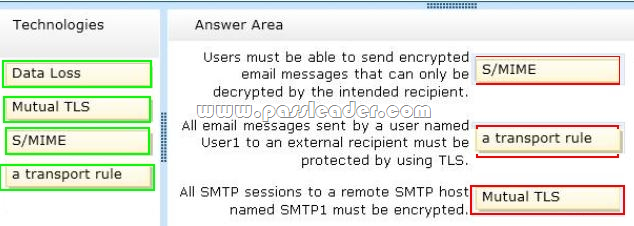
QUESTION 68
Drag and Drop Question
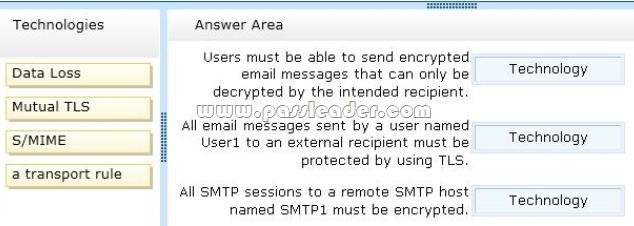
You have an Exchange Server 2013 organization. Your company identifies the following security requirements:
– Users must be able to send encrypted email messages that can only be decrypted by the intended recipient.
– All email messages sent by a user named User1 to an external recipient must be protected by using TLS.
– All SMTP sessions to a remote SMTP host named SMTP1 must be encrypted.
You need to recommend which technology must be used to meet each requirement. Which technologies should you recommend? (To answer, drag the appropriate technologies to the requirements in the answer area. Each technology may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.)
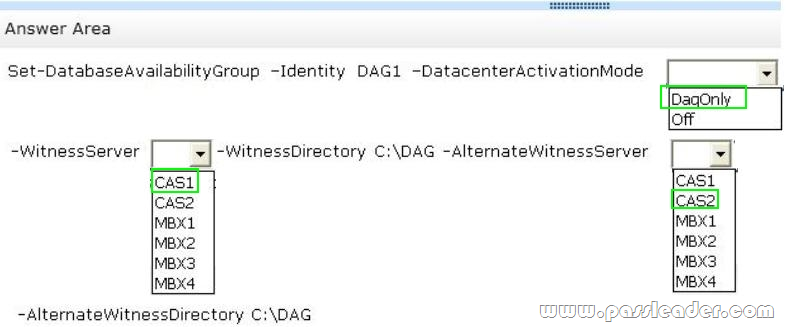
QUESTION 69
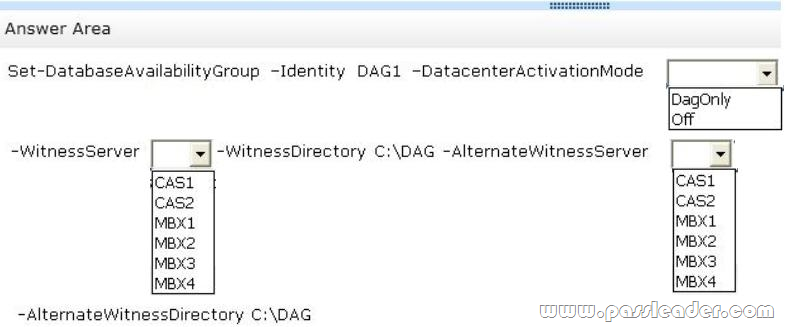
Hotspot Question
Your company has a main office and a disaster recovery site. An Active Directory site named MainSite exists for the main office. An Active Directory site named DRSite exists for the disaster recovery site. The two sites connect to each other by using a WAN link. All users work in the main office. You have an Exchange Server 2013 organization. The organization contains six servers. The servers are configured as shown in the following table.
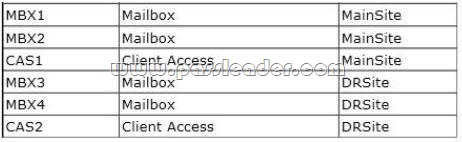
All of the Mailbox servers are members of a database availability group (DAG) named DAG1. After a WAN link failure, you discover that all of the active mailbox database copies are located on MBX3, even though MBX1 and MBX2 are still running. You need to prevent an automatic failover of DAG1 if the WAN link between the two sites fails but the servers in both sites are still running. The solution must prevent two active copies of the same database. What should you do? (To answer, select the appropriate options in the answer area.)
QUESTION 70
You have an Exchange Server 2010 organization that contains three servers. The servers are configured as shown in the following table.
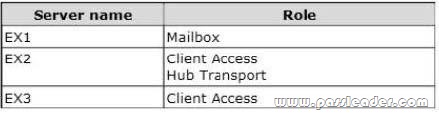
Microsoft Outlook is configured to connect to an FQDN of mail.adatum.com. Mail.adatum.com resolves to the IP address of a Layer 7 hardware load balancer. The hardware load balancer is configured to send traffic to EX2 and EX3. You deploy an Exchange Server 2013 Mailbox server and an Exchange Server 2013 Client Access server. You plan to migrate all mailboxes to Exchange Server 2013. You need to recommend a solution to ensure that users can access their mailbox on EX1 or EX4 during the migration. What should you do?
A. Create a Client Access server array that contains EX1 and EX5.
B. Modify the autodiscover.contoso.com resource record to point to EX5.
C. Modify the properties of the hardware load balancer to point to EX5.
D. Create a DNS record named legacy.contoso.com in the internal DNS zone.
Answer: C
Explanation:
Note: So what is the Client Access server in Exchange 2013?
The Client Access server role is comprised of three components, client protocols, SMTP, and a UM Call Router. The CAS role is a thin, protocol session stateless server that is organized into a load balanced configuration. Unlike previous versions, session affinity is not required at the load balancer (but you still want a load balancer to handle connection management policies and health checking). This is because logic now exists in CAS to authenticate the request, and then route the request to the Mailbox server that hosts the active copy of the mailbox database. The Mailbox server role now hosts all the components and/or protocols that process, render and store the data. No clients will ever connect directly to the Mailbox server role; all client connections are handled by the Client Access server role.
Reference:
Exchange 2013 Server Role Architecture.
QUESTION 71
Your company has three data centers. The data centers are located in Montreal, New York, and Seattle. You have an Exchange Server 2013 organization that contains six servers. The servers are configured as shown in the following table.
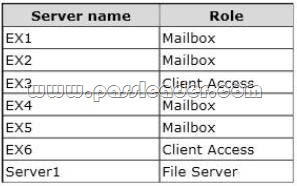
The organization is configured as shown in the following exhibit. (Click the Exhibit button.)
The file share witness for DAG1 is located on EX3. You plan to implement site resiliency and use a single name space named mail.contoso.com. You need to recommend a solution to minimize the amount of time that the Exchange Server services are unavailable if either the data center in Montreal or the data center in Seattle fails. Which two tasks should you recommend performing? (Each correct answer presents part of solution. Choose two.)
A. Deploy a hardware load balancer to EX3 and EX6.
B. Create two DNS host (A) records for mail.contoso.com.
C. Configure EX6 as an alternate file share witness.
D. Move the file share witness to Server1.
Answer: AD
Explanation:
Load balancing serves two primary purposes. It reduces the impact of a single Client Access server failure within one of your Active Directory sites. In addition, load balancing ensures that the load on each of your Client Access servers is evenly distributed.
QUESTION 72
You have an Exchange Server 2013 organization. You create a data loss prevention (DLP) policy. The mode of the DLP policy is set to Enforce. You need to ensure that email messages containing social security numbers from the United States are blocked. Which two possible rules achieve this goal? (Each correct answer presents a complete solution. Choose two.)
A. U.S. State Breach: Allow Override
B. U.S. State Breach: Scan email sent outside – low count
C. U.S. State Breach: Scan email sent outside – high count
D. U.S. State Breach: Scan text limit exceeded
E. U.S. State Breach: Attachment not supported
Answer: BC
Explanation:
Note:
* In Microsoft Exchange Server 2013, you can use data loss prevention (DLP) policy templates to help meet the messaging policy and compliance needs of your organization. These templates contain pre-built sets of rules that can help you manage message data that is associated with several common legal and regulatory requirements.
* DLP policy templates in Exchange include:
U.S. State Breach Notification Laws. Helps detect the presence of information subject to U.S. State Breach Notification Laws, including data like social security and credit card numbers.
http://blogs.msdn.com/b/microsoft_press/archive/2013/04/29/from-the-mvps-data-loss-prevention-with-office-365-and-exchange-online.aspx
QUESTION 73
You have an Exchange Server 2013 organization. You purchase a Microsoft Office 365 subscription and configure a hybrid deployment. The network contains an SMTP relay server named smarthost.contoso.com. The server is configured to use a certificate that has a subject name of smarthost.contoso.com. All users have Microsoft Outlook 2013 installed on their client computer. Outlook 2013 is configured to connect to mail.contoso.com. All Exchange servers have a certificate that has a subject name of mail.contoso.com. You discover that email messages sent from on-premises users are not delivered to Office 365 recipients. You discover that the Send connector for Office 365 uses a smart host of smarthost.contoso.com. You need to ensure that the on-premises users can send email messages to the Office 365 recipients. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. Run the Hybrid Configuration Wizard again.
B. Configure the Microsoft Exchange Online Protection (EOP) Send connector to use smarthost.contoso.com.
C. Configure the centralized mail transport option.
D. Remove the smart host from the Send connector.
E. Assign a certificate that has a subject name of smarthost.contoso.com to the Send connector.
Answer: AE
Explanation:
A:
Creating and configuring a hybrid deployment with the Hybrid Configuration wizard is now a single process in Microsoft Exchange Server 2013. First, the wizard creates the HybridConfiguration object in your on-premises Active Directory. This Active Directory object stores the hybrid configuration information for the hybrid deployment and is updated by the Hybrid Configuration wizard. Next, the wizard gathers existing on- premises Exchange and Active Directory topology configuration data, Office 365 tenant and Exchange Online configuration data, defines several organization parameters and then runs an extensive sequence of configuration tasks in both the on-premises and Exchange Online organizations.
E:
Note:
* By default, Microsoft Exchange Server 2013 doesn’t allow you to send mail outside of your domain. To send mail outside your domain, you need to create a Send connector.
* Use the Set-SendConnector cmdlet to modify a Send connector.
Parameters include TlsCertificateName. The TlsCertificateName parameter specifies the X.509 certificate to use with TLS sessions and secure mail. Valid input for this parameter is [I]Issuer[S]Subject. The Issuer value is found in the certificate’s Issuer field, and the Subject value is found in the certificate’s Subject field. You can find these values by running the Get-ExchangeCertificate cmdlet.
Incorrect:
Not B:
Microsoft Exchange Online Protection is not required here.
QUESTION 74
You have a server named Server1 that has Exchange Server 2013 installed. Users access their mailbox by using Microsoft Outlook 2010 and Outlook Web App. You enable auditing for all of the mailboxes. You need to identify when a mailbox is accessed by someone other than the owner of the mailbox. What are two possible ways to achieve this goal? (Each correct answer presents a complete solution. Choose two.)
A. Export the administrator audit log.
B. Run an administrator role group report.
C. Export the mailbox audit log.
D. Run a non-owner mailbox access report.
E. Review the security event log.
Answer: CD
Explanation:
C:
Use the Auditing tab to run reports or export entries from the mailbox audit log and the administrator audit log.
– The mailbox audit log records whenever a mailbox is accessed by someone other than the person who owns the mailbox. This can help you determine who has accessed a mailbox and what they have done.
– The administrator audit log records any action, based on a Windows PowerShell cmdlet, performed by an administrator. This can help you troubleshoot configuration issues or identify the cause of security- or compliance-related problems.
D:
Run a Non-Owner Mailbox Access Report. Use this report to find mailboxes that have been accessed by someone other than the person who owns the mailbox.
QUESTION 75
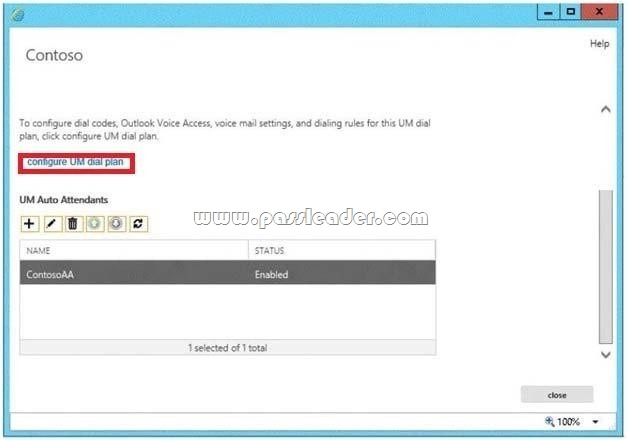
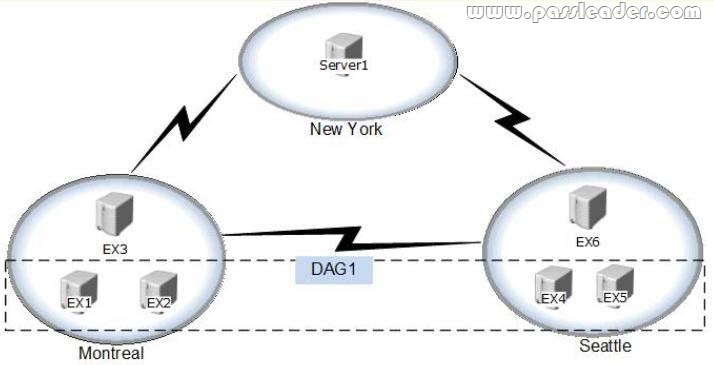
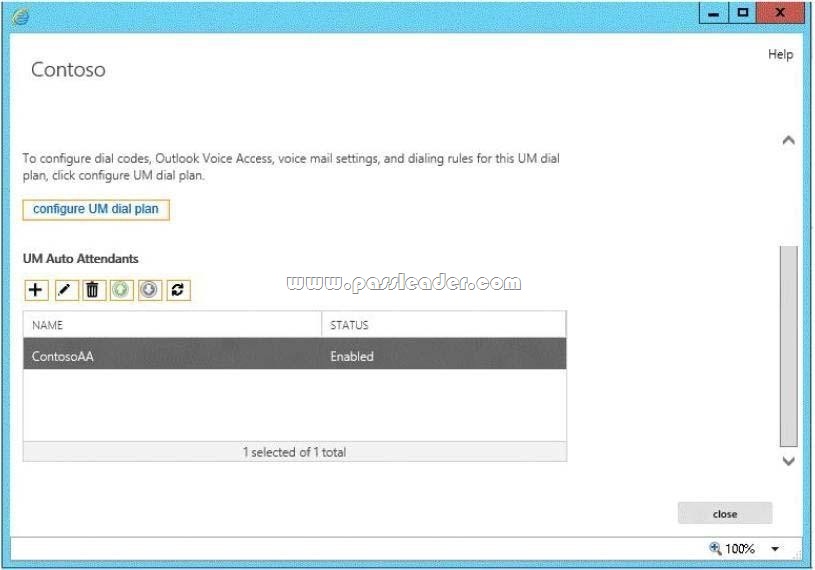
Hotspot Question
Your company implements Exchange Server 2013 Unified Messaging (UM). The company uses an auto attendant. You need to ensure that when calls are routed to the auto attendant, callers can press 0 to reach a receptionist. Which option should you configure from the UM Auto Attendant window? To answer, select the appropriate option in the answer area.
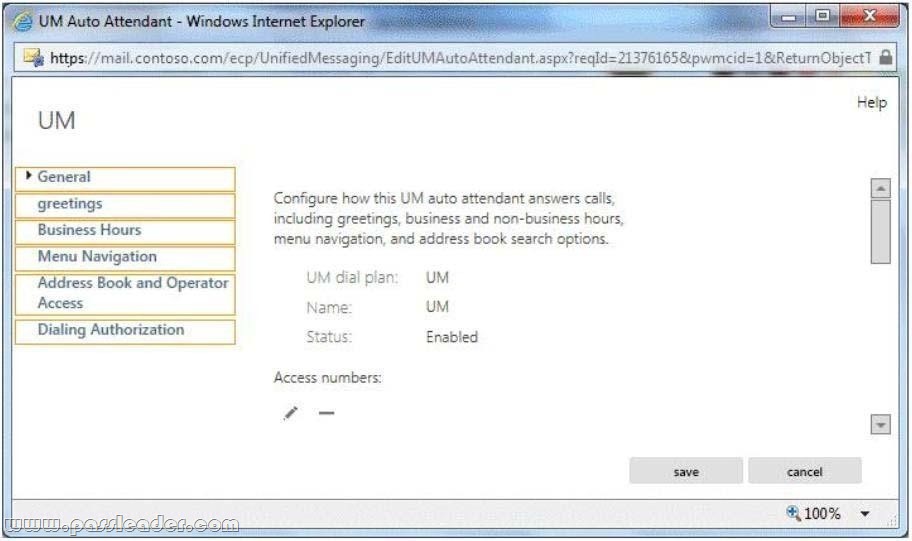
Answer:
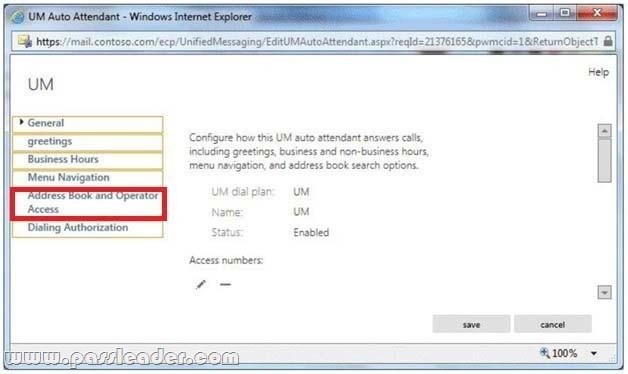
Explanation:
http://technet.microsoft.com/en-us/library/bb232201%28v=exchg.141%29.aspx
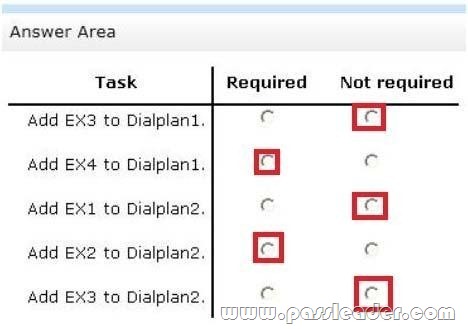
QUESTION 76
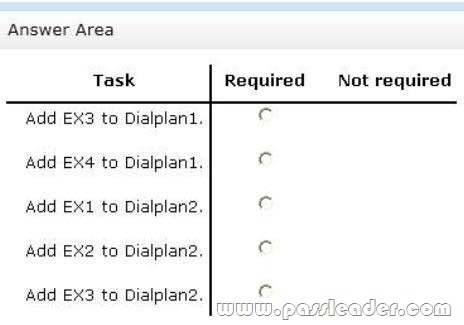
Hotspot Question
You have an Exchange Server organization that contains four servers. The servers are configured as shown in the following table.

SiteA contains an IP gateway that uses a dial plan named Dialplan1. SiteB contains a Lync Server 2013 server that uses a dial plan named Dialplan2. You plan to migrate all Unified Messaging (UM) functionalities to Exchange Server 2013. You need to identify which tasks must be performed to complete the migration. Which tasks should you identify? (To answer, select the tasks that are required and not required in the answer area.)
QUESTION 77
Hotspot Question
You have an Exchange Server 2013 organization. All users are enabled for Unified Messaging (UM) and access their voice mail by using Microsoft Lync 2010. Callers report that when they press a key to dial an external telephone number, they hear a message indicating that the intended destination cannot be reached. You need to ensure that the callers can reach the external number successfully. What should you modify? To answer, select the appropriate object in the answer area.
QUESTION 78
You have an Exchange Server 2013 organization. You successfully migrate the public folders from a previous version of Exchange Server. You discover that one of the public folder mailboxes almost reached its quota size. You need to move some of the public folders in the public folder mailbox to another public folder mailbox. What should you run?
A. Update-PublicFolderMailbox
B. New-PublicFolderMoveRequest
C. New-PublicFolderMigrationRequest
D. Set-PublicFolderMailbox
Answer: B
Explanation:
You can either perform a publicfoldermoverequest, or run the splitpublicfoldermailbox.ps1 script.
* If the content of a public folder mailbox begins to exceed your mailbox quotas, you may need to move public folders to a different public folder mailbox. There are a couple ways to do this. To move one or more public folders that don’t contain subfolders, you can use the PublicFolderMoveRequest cmdlets.
* Use the New-PublicFolderMoveRequest cmdlet to begin the process of moving public folder contents between public folder mailboxes. Moving public folders only moves the physical contents of the public folder; it doesn’t change the logical hierarchy. When the move request is completed, you must run the Remove-PublicFolderMoveRequest cmdlet to remove the request or wait until the time specified in the CompletedRequestAgeLimit parameter has passed. The request must be removed before you can run another move request.
Incorrect:
Not A: Use the Update-PublicFolderMailbox cmdlet to update the hierarchy for public folders.
Not C: Use the New-PublicFolderMigrationRequest cmdlet to begin the process of migrating public folders from Microsoft Exchange Server 2007 or Exchange Server 2010 to Exchange Server 2013.
Reference:
Move a Public Folder to a Different Public Folder Mailbox.
QUESTION 79
Your company has three offices. Each office has 1,000 users and is configured as an Active Directory site. Each site connects directly to the Internet. The network contains six servers that have Exchange Server 2013 installed. The servers are configured as shown in the following table.
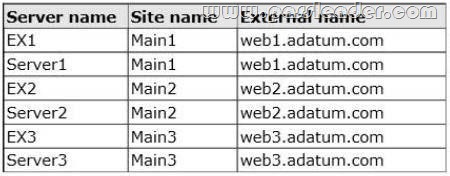
An administrator performs a datacenter switchover by changing the DNS record for webl.adatum.com to point to the IP address of web2.adatum.com. Users from Main1 report that when they connect to Outlook Web App, they receive a certificate warning message. You need to recommend a solution to ensure that the users do not receive a certificate warning message when a datacenter switchover is performed. What should you include in the recommendation?
A. Three host headers for the Default Web Site on each Client Access server
B. One certificate that contains all of the external names as subject alternative names
C. Three certificates that each contains one of the external names
D. An external URL for each Client Access server set to $null
Answer: B
Explanation:
IRM also helps allow or restrict recipient actions such as forwarding a message to other recipients, printing a message or attachment, or extracting message or attachment content by copying and pasting.
http://technet.microsoft.com/en-us/library/dd638140%28v=exchg.150%29.aspx
QUESTION 80
You have an Exchange Server 2010 organization named adatum.com. All public folders are stored on a server named EX5. You deploy a new server named EX6. EX6 has Exchange Server 2013 installed. You move all mailboxes to EX6. You need to move the public folders to EX6. The solution must ensure that users can access the public folders after EX5 is decommissioned. Which two actions should you perform? (Each correct answer presents part of the solution. Choose two.)
A. On EX6, create a public folder mailbox.
B. On EX6, run the New-PublicFolderMigrationRequest cmdlet.
C. On EX5, modify the replication partners for all of the public folders.
D. On EX6, run the New-SiteMailboxProvisioningPolicy cmdlet.
E. On EX5, assign the FolderOwner permission to the Public Folder Management management role group for all of the public folders.
F. On EX6, run the MoveAllReplicas.ps1 script.
Answer: AB
Explanation:
B:
Use the New-PublicFolderMigrationRequest cmdlet to begin the process of migrating public folders from Microsoft Exchange Server 2007 or Exchange Server 2010 to Exchange Server 2013.
Note: See step 4 and 5 below:
Step 1: Download the migration scripts
Step 2: Prepare for the migration
Step 3: Generate the .csv files
Step 4: Create the public folder mailboxes on the Exchange 2013 server Step 5: Start the migration request
Example:
New-PublicFolderMigrationRequest -SourceDatabase (Get-PublicFolderDatabase -Server <Source server name>) -CSVData (Get-Content <Folder to mailbox map path> -Encoding Byte) -BadItemLimit $BadItemLimitCount
Step 6: Lock down the public folders on the legacy Exchange server for final migration (downtime required)
Step 7: Finalize the public folder migration (downtime required)
Step 8: Test and unlock the public folder migration
http://technet.microsoft.com/en-us/library/jj150538%28v=exchg.150%29.aspx#MigratePFs
Get the newest PassLeader 70-342 VCE dumps here: http://www.passleader.com/70-342.html (233 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-342 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpfnExREVzWWtnTGZYZDhiVm1ESjV2dkgwU09EOExRMloxUE95aUdnWC1lUU0